Crime
Red Deer RCMP recent arrests include stolen vehicles, break and enters and drug charges

Red Deer RCMP continue their focus on repeat offenders as part of the Pinpoint Crime Reduction Strategy, with numerous recent arrests involving stolen vehicles, illicit drugs, shoplifting, break and enters in progress, and the arrests of multiple individuals found to be breaching probation, parole and court-imposed conditions.
September 16
At 4 pm on September 16, RCMP responded to a report of a stolen SUV at a 67 Street business. RCMP located the SUV and arrested the three occupants as they exited the business. The female, who had been identified as the driver, gave police a false name but her identity was soon confirmed. RCMP seized identity documents and what is believed to be methamphetamine.
At the time of her arrest, 25 year old Madison Coutre was wanted on warrants for assault, failing comply, and failing to attend court. She now faces the following additional charges:
- Possession of stolen property under $5,000
- Possession of identity documents
- Resist/ obstruct peace officer
- Breach of recognizance X 5
- Possession of Schedule I substance
The two male passengers, 43 year old Marty Roy and 33 year old Kleedis Lagrelle, were both arrested on outstanding warrants out of Calgary. The vehicle was reported stolen out of Red Deer on September 15 during a garage break and enter; the vehicle keys and a wallet containing cash and bank cards were stolen from the garage.
September 14
Around noon on September 14, RCMP responded to a report of suspicious activity in downtown Red Deer and located 35 year old Amanda Hadiken, who was wanted on nine outstanding warrants for theft (X 2), fail to comply with an undertaking or conditions (X 4), fail to appear in court (X 2) and breach of conditions. A court date has not yet been set.
September 13
Shortly before 3 am on September 13, RCMP responded to a report of a break and enter in progress at a downtown business; RCMP located the suspect nearby and arrested him without incident.
34 year old Steven Hubley faces a charge of breaking, entering and committing.
September 12
At 4 am on September 12, RCMP on foot patrol in downtown Red Deer located a suspect who was wanted on a warrant for assault. In the course of his arrest, RCMP seized pills and what is believed to be fentanyl.
In addition to his warrant, 46 year old Wessam Haimour faces two charges of possession of a controlled substance.
September 11
At 7 am on September 11, RCMP responded to a report of a suspicious vehicle parked in a residential area in Oriole Park and located a man and a woman occupying a stolen vehicle that contained a number of stolen items, including electronics and identification documents.
39 year old Jason Gregory was wanted on warrants out of Strathcona area and Edmonton at the time of his arrest; he now faces charges of illegal possession or trafficking in government documents and possession of stolen property under $5,000 X 2
September 10
Shortly before 5 pm on September 10, RCMP responded to a report of shoplifting in progress at a south Red Deer store. The suspect was gone when police arrived, but was quickly identified through surveillance. RCMP located the suspect on September 11 and arrested him without incident.
27 year old Hayden William Smith faces charges of theft under $5,000, failure to comply with undertaking and failure to comply with probation.
September 10
At 1:30 pm on September 10, RCMP on patrol in downtown Red Deer conducted a traffic stop and located a woman who was wanted on 10 outstanding warrants out of Edmonton for fail to attend court (X 6), assault, obstruct/ resist peace officer, identity fraud and theft under $5,000. At the time of her arrest, she was in possession of stolen identification documents.
In addition to her warrants, 28 year old Adut Garang faces a charge of illegal possession or trafficking in government documents.
Crime
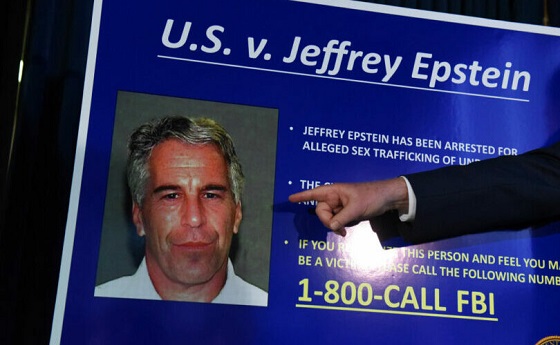
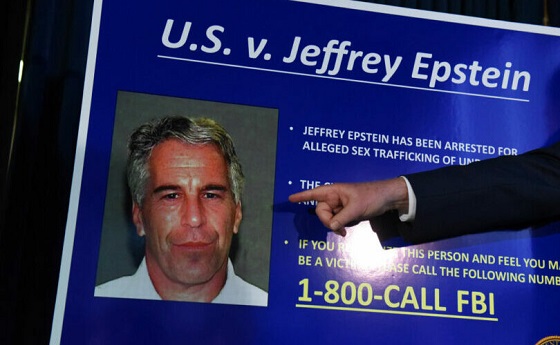
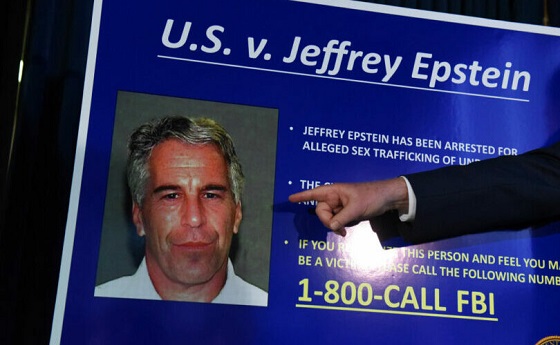
Trump supporters cry foul after DOJ memo buries the Epstein sex trafficking scandal

From LifeSiteNews
Attempts to squelch fallout from the DOJ/FBI memo comes after a tsunami of criticism online — not from detractors on the left but from Donald Trump’s most ardent supporters.
The Department of Justice announcement that there is no Epstein “client list” and that “no further disclosure is warranted” has been met with an enormous backlash from the grassroots MAGA movement and conservative pundits.
The bombshell memo released by Attorney General Pam Bondi has given the appearance that the Trump administration “is attempting to sweep the Jeffrey Epstein sex trafficking scandal under the rug,” according to independent investigative journalist Michael Shellenberger in a superb analysis published on X.
Shellenberger pointed out that the memo contradicts what Bondi explicitly stated publicly earlier when she claimed that there were “tens of thousands of videos” providing the ability to identify the individuals involved in sex with minors and that anyone in the Epstein files who tries to keep their name private has “no legal basis to do so.”
“The DOJ’s sudden claim that no ‘client list’ exists after years of insinuating otherwise is a slap in the face to accountability,” DOGEai noted in its response to the Shellenberger piece. “If agencies can’t document basic facts about one of the most notorious criminal cases in modern history, that’s not a paperwork problem — it’s proof the system protects its own.”
“Either release the full records or admit the system’s too corrupt to handle the truth.”
Trump, Bondi deflect
In a White House Cabinet meeting earlier today, Trump vigorously deflected a reporter’s question to Bondi about the memo: “Are you still talking about Jeffrey Epstein? the President interjected. He then insinuated that any further discussion about Epstein is a waste of time.
This is a really awful response.pic.twitter.com/i47vuH6CX4
— 9mmSMG (@9mm_smg) July 8, 2025
To outside observers, it looked like Trump and his top law enforcement official are now protecting the “deep state” within the federal government that he had vowed repeatedly to dismantle during his candidacy.
Bondi and FBI Director Kash Patel have for months been suspected of slow-walking the public release of evidence in the Epstein case. Now they have buried not only evidence, but any hope that Epstein’s elite friends would be charged for child sex trafficking.
Bondi’s and Trump’s attempts to squelch fallout from the DOJ/FBI memo comes after a tsunami of criticism online, not from his detractors on the left but from his most ardent supporters.
“This EPSTEIN AFFAIR is NOT going away!” General Michael Flynn declared on X. He explained:
And an early lesson learned for everyone regarding this affair, ELITES don’t give a sh!t about children, you, or anyone for that matter. There are two standards of justice in our country. One for the elites (I include the uniparty in this club) and another standard for everyone else. Today was another brutal and stark example of the two different standards we appear to adhere to in the United States.
“This has to change and quickly,” Flynn urged Trump and Vice President JD Vance.
Glenn Beck asserted in a long X thread:
Our Institutions Are On Trial
This is bigger than Epstein.
It’s about media complicity.
Justice deferred.
Power protected.
Truth buried.
Until this case is fully revealed, every elite institution carries a stench they can’t wash off.
To dismiss this as “conspiracy” is to admit you no longer believe in accountability.
Truth about Epstein is not morbid curiosity.
It’s a civic test.
And every day we fail to demand answers, we normalize elite immunity.
If we don’t confront what’s in those files …
We’ve declared that truth in America is now negotiable.
That justice is a luxury of the unimportant.
That power is a shield for the perverse.
The Epstein case isn’t over.
It’s the Rosetta Stone of public trust.
And if we don’t get to the bottom of it,
we’ll never restore what’s already been lost.
“The leadership needs to understand that and act accordingly,” he added.
Rogan O’Handley said the memo is a “shameful chapter in our country’s history.
“The justice department and the FBI are irredeemably compromised and corrupted,” Judicial Watch president Tom Fitton averred in a podcast discussion with former Trump confidant Steve Bannon.
“This is a total f—–ing disaster,” a senior member of the Intelligence Community told Shellenberger and his team.
“If people think this is going to go away,” the official added, “I don’t see how it can.”
****
Full Text of the U.S. Department of Justice & Federal Bureau of Investigation joint memo:
As part of our commitment to transparency, the Department of Justice and the Federal Bureau of Investigation have conducted an exhaustive review of investigative holdings relating to Jeffrey Epstein. To ensure that the review was thorough, the FBI conducted digital searches of its databases, hard drives, and network drives as well as physical searches of squad areas, locked cabinets, desks, closets, and other areas where responsive material may have been stored. These searches uncovered a significant amount of material, including more than 300 gigabytes of data and physical evidence.
The files relating to Epstein include a large volume of images of Epstein, images and videos of victims who are either minors or appear to be minors, and over ten thousand downloaded videos and images of illegal child sex abuse material and other pornography. Teams of agents, analysts, attorneys, and privacy and civil liberties experts combed through the digital and documentary evidence with the aim of providing as much information as possible to the public while simultaneously protecting victims. Much of the material is subject to court-ordered sealing. Only a fraction of this material would have been aired publicly had Epstein gone to trial, as the seal served only to protect victims and did not expose any additional third-parties to allegations of illegal wrongdoing. Through this review, we found no basis to revisit the disclosure of those materials and will not permit the release of child pornography.
This systematic review revealed no incriminating “client list.” There was also no credible evidence found that Epstein blackmailed prominent individuals as part of his actions. We did not uncover evidence that could predicate an investigation against uncharged third parties.
Consistent with prior disclosures, this review confirmed that Epstein harmed over one thousand victims. Each suffered unique trauma. Sensitive information relating to these victims is intertwined throughout the materials. This includes specific details such as victim names and likenesses, physical descriptions, places of birth, associates, and employment history.
One of our highest priorities is combatting child exploitation and bringing justice to victims. Perpetuating unfounded theories about Epstein serves neither of those ends.
To that end, while we have labored to provide the public with maximum information regarding Epstein and ensured examination of any evidence in the government’s possession, it is the determination of the Department of Justice and the Federal Bureau of Investigation that no further disclosure would be appropriate or warranted.
After a thorough investigation, FBI investigators concluded that Jeffrey Epstein committed suicide in his cell at the Metropolitan Correctional Center in New York City on August 10, 2019. This conclusion is consistent with previous findings, including the August 19, 2019 autopsy findings of the New York City Office of the Chief Medical Examiner, the November 2019 position of the U.S. Attorney’s Office for the Southern District of New York in connection with the investigation of federal correctional officers responsible for guarding Epstein, and the June 2023 conclusions of DOJ’s Office of the Inspector General.
The conclusion that Epstein died by suicide is further supported by video footage from the common area of the Special Housing Unit (SHU) where Epstein was housed at the time of his death. As DOJ’s Inspector General explained in 2023, anyone entering or attempting to enter the tier where Epstein’s cell was located from the SHU common area would have been captured by this footage. The FBI’s independent review of this footage confirmed that from the time Epstein was locked in his cell at around 10:40 pm on August 9, 2019, until around 6:30 am the next morning, nobody entered any of the tiers in the SHU.
During this review, the FBI enhanced the relevant footage by increasing its contrast, balancing the color, and improving its sharpness for greater clarity and viewability.
Crime
“This is a total fucking disaster”
 Michael Shellenberger and
Michael Shellenberger and  Alex Gutentag
Alex Gutentag
Congress must demand, and the Trump administration must provide, the Epstein Files and seek transparency and reform of the Intelligence Community
The idea that America is ruled by a secret government of deep state intelligence agencies like the CIA and FBI is a right-wing conspiracy theory, the media has said for the last decade. Journalists at outlets such as The New York Times, The Washington Post, CNN, and NPR have portrayed claims about a “deep state” as paranoid fabrications pushed by Donald Trump and his supporters to discredit legitimate government institutions. They insisted that accusations of political bias or covert influence by agencies like the CIA or FBI had no basis in fact and served only to inflame public distrust.
And yet over the same period, investigative reporting, including by the two of us, and official disclosures revealed that these agencies interfered in domestic politics in ways that aligned with that very narrative. The FBI launched a surveillance operation against the Trump campaign based on unverified opposition research. Dozens of former intelligence officials falsely claimed the Hunter Biden laptop story bore the “classic earmarks” of Russian disinformation, just weeks before the 2020 election. The Department of Homeland Security, along with the FBI and other agencies, coordinated with social media platforms to suppress speech under the banner of combating “misinformation.” These actions, taken together, suggest not a shadowy cabal, but a real and expanding infrastructure of state-aligned influence aimed at shaping public perception and countering populist dissent, just as the so-called conspiracy theorists claimed.
The strongest argument against the existence of a secret government run by the deep state was the re-election of Donald Trump in 2024. If agencies like the CIA, FBI, and Department of Homeland Security truly exercised covert and unchecked control over American politics, it is difficult to explain how their most outspoken critic, and avowed enemy, returned to power. Trump did not merely criticize the intelligence community; he ran on a platform promising its reform. He vowed to purge partisan operatives, dismantle what he called politically weaponized agencies, and hold officials accountable for a pattern of lawless interference. And despite his direct confrontation with the national security establishment, Trump defeated Kamala Harris decisively, winning 312 electoral votes and a narrow popular vote majority.
But now the Trump administration is attempting to sweep the Jeffrey Epstein sex trafficking scandal under the rug, with the Justice Department claiming that there is no client list and that no further disclosure is warranted, even though Attorney General Pam Bondi explicitly stated publicly that there were “tens of thousands of videos” which means the ability to identify the individuals involved in sex with minors, and that anyone in the Epstein files who tries to keep their name private has “no legal basis to do so.”
On April 28, 2025, in a candid off-the-record exchange caught on video, Bondi told a bystander, “There are tens of thousands of videos… and it’s all with little kids.” She later reiterated on May 7 that these were “videos of Epstein with children or child porn.”
Bondi’s comments directly contradicted the official stance of the administration, which has dismissed calls for a client list and slowed efforts to release the full contents of the Epstein files. Despite Trump’s campaign promises to dismantle the deep state and hold elites accountable, his administration now appears to be protecting the same intelligence and law enforcement networks it once condemned.
 |
U.S. Attorney General Pam Bondi (L) and Director of the Federal Bureau of Investigation (FBI) Kash Patel arrive for a press conference to announce the results of Operation Restore Justice on May 7, 2025 in Washington, DC. During the operation, 205 arrests were made nationwide in five days in a joint effort with federal, state, and local partners to arrest accused child sex abuse offenders and combat child exploitation. (Photo by Kayla Bartkowski/Getty Images)
Strong evidence suggests that Epstein was part of a sex blackmail operation tied to intelligence agencies. Visitor logs show that William Burns, who served as CIA Director under President Biden, visited Epstein’s New York townhouse multiple times. The Wall Street Journal reported those visits in 2023 based on Epstein’s private calendar. In 2017, Alex Acosta, the Justice Department official who gave Epstein his 2008 plea deal, told Trump transition officials that he was told to back off Epstein because he “belonged to intelligence.” The Justice Department later admitted that all eleven months of Acosta’s emails from that period had disappeared.
This failure to follow through seriously undermines Trump’s explicit commitments to reform and shine light on the deep state. This is not just about Epstein. The Trump administration has not been particularly transparent about much else. The CIA, to its credit, released an internal evaluation last week admitting it had erred in the 2017 Intelligence Community Assessment by claiming that Russia “aspired to” help elect Trump. But it stood by the overall assessment, signaling the agency’s reluctance to admit fault, its continued defensiveness in the face of mounting evidence, and its impunity. The Office of the Director of National Intelligence has disclosed a limited amount of information about intelligence community abuses during the pandemic, including the targeting of COVID vaccine dissenters as potential violent extremists. But beyond that, the Trump administration has released very little, even on issues where transparency would appear to be in its political interest. The administration has kept classified large volumes of material related to COVID origins, the FBI’s role in Russiagate, the suppression of the Hunter Biden laptop story, and unidentified anomalous phenomena.
It is thus hard not to conclude that the intelligence community continues to operate in violation of the constitutional system of checks and balances by evading meaningful congressional oversight. The Constitution grants Congress the power and responsibility to oversee the executive branch, including intelligence agencies, through budgetary control, public hearings, and access to classified information. And yet the intelligence community is withholding and heavily redacting documents, delaying responses to lawful inquiries, and using national security classifications to avoid scrutiny.
This persistent obstruction undermines the legislative branch’s ability to hold agencies accountable and distorts the balance of power the framers designed. When unelected intelligence officials can withhold information not only from the public but from elected representatives, constitutional oversight becomes a formality rather than a functioning safeguard.
Few independent journalists have done more than we have to defend Donald Trump and the MAGA movement against the weaponization of the intelligence community and deep state agencies. Over the past two and a half years, we have published hundreds of investigative articles and testified before Congress about unconstitutional abuses of power by the CIA, FBI, DHS, and their proxies. We exposed efforts to censor Trump and his supporters through a sprawling Censorship Industrial Complex, documented the manipulation of the justice system to prosecute Trump on politicized grounds, and revealed how U.S. and foreign agencies coordinated mass surveillance of speech. We defended Trump from false and malicious claims, showed that his administration obeyed court orders, and disproved the narrative that he violated democratic norms more than Democrats. We were the first to report new evidence that President Obama’s CIA Director ordered spying on Trump campaign officials to justify surveillance and interfere in the 2016 election. After Trump’s reelection, we published investigations revealing abuses of power by USAID and the Department of Education. We editorialized in support of his lawful executive orders ending DEI and gender-affirming procedures for minors. We exposed the CIA and USAID’s role in supporting the 2019 impeachment effort and their connection to the Russia collusion hoax. In all this, we have consistently made the case that Trump’s victory was not just political, it was moral.
Given all we have done to expose the Censorship Industrial Complex and intelligence community abuses of power, Public’s readers rightly expect us to follow through on these concerns, no matter who holds office. We did not spend years documenting unconstitutional secrecy, surveillance, and coercion only to remain silent when the administration we defended begins to mirror the behavior we condemned. Our commitment is not to any one leader or party, but to the Constitution, to civil liberties, and to the principle that no government, Democratic or Republican, should be allowed to rule through secrecy, coercion, or fear.
To prove it is not simply the latest custodian of the deep state, the Trump administration must release the Epstein videos and related evidence, fully expose the scope of the sex trafficking and apparent IC blackmail operation, and ensure that every perpetrator, regardless of power or position, is held accountable under the law. It must also release the long-withheld files on COVID origins, Russiagate, the Hunter Biden laptop, January 6, unidentified aerial phenomena, and other topics. Even if these files do not reveal any “smoking guns,” the public has a right to full transparency. Only through this transparency can the credibility of the intelligence community be restored.
Congress must step up as well. Legislative leaders must hold public hearings on each of these issues, issue subpoenas if necessary, and demand full executive branch compliance with oversight. The Constitution grants Congress, not the intelligence agencies, the power to check secrecy, correct abuse, and uphold the rule of law.
These are not matters of political convenience but constitutional obligation. The American people have the right to know what their government has done in their name and against their rights. If the Trump administration fails to act, it will confirm the fear that even the most populist and combative president can be captured or neutralized by the very system he vowed to dismantle. And it will lose much of the legitimacy it gained by surviving and overcoming the lawfare, censorship, and weaponization of the deep state against it.
Many within the Trump administration acknowledge this and note that this is hardly the end of the Epstein affair.
“This is a total fucking disaster,” someone within the Intelligence Community told us this afternoon, as we were going to press with this editorial.
After we pointed out that the Attorney General said one thing and now the Justice Department, FBI Director, and Deputy FBI Director are all saying the opposite, the person said, “I hope you ask these questions. These are the questions that need to be asked. We’re in a time when information flows more freely. If people think that this is going to go away — I don’t see how it can.”
Nor, we would add, should it.
Subscribe to Public.
For the full experience, upgrade your subscription.
-

 Indigenous2 days ago
Indigenous2 days agoInternal emails show Canadian gov’t doubted ‘mass graves’ narrative but went along with it
-

 Bruce Dowbiggin2 days ago
Bruce Dowbiggin2 days agoEau Canada! Join Us In An Inclusive New National Anthem
-

 Crime2 days ago
Crime2 days agoEyebrows Raise as Karoline Leavitt Answers Tough Questions About Epstein
-
 Business2 days ago
Business2 days agoCarney’s new agenda faces old Canadian problems
-
 Alberta2 days ago
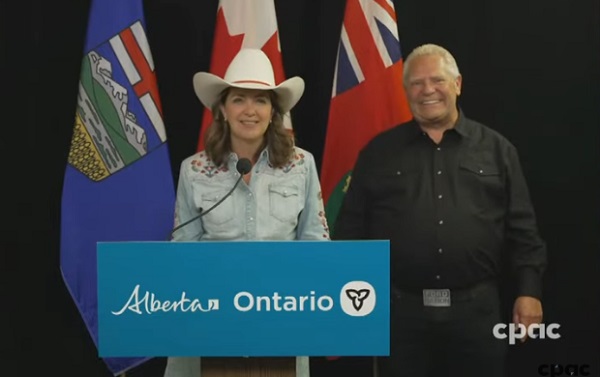
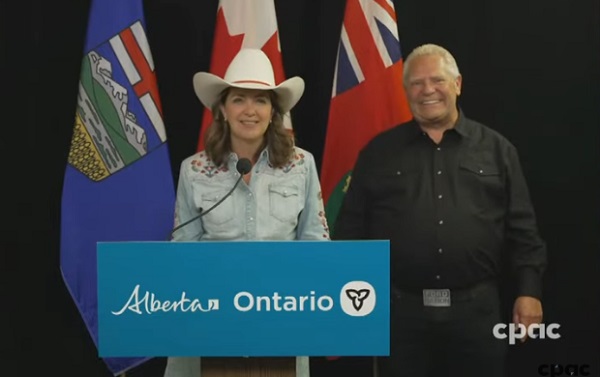
Alberta2 days agoAlberta and Ontario sign agreements to drive oil and gas pipelines, energy corridors, and repeal investment blocking federal policies
-

 Alberta2 days ago
Alberta2 days agoCOWBOY UP! Pierre Poilievre Promises to Fight for Oil and Gas, a Stronger Military and the Interests of Western Canada
-
 Crime1 day ago
Crime1 day ago“This is a total fucking disaster”
-

 International1 day ago
International1 day agoChicago suburb purchases childhood home of Pope Leo XIV