Crime
Major bust nets a million in drugs and cash

Project Embrace Makes 6 Arrests,
$1 Million in Seizures
Edmonton… A drug trafficking network that spanned Alberta and British Columbia has been dismantled. ALERT’s Project Embrace has resulted in the arrest of six suspects and the seizure of over $1 million worth of drugs and cash.
Project Embrace was a nine-month investigation that targeted all facets of the suspected criminal network’s operation, including supply, distribution, and street-level sales. ALERT Edmonton’s organized crime team led the investigation with the assistance of British Columbia’s Combined Forces Special Enforcement Unit and Bonnyville RCMP.
More than six kilograms of cocaine and two kilograms of methamphetamine were seized, along with more than $342,000 in cash. In addition, half a dozen suspects were charged, with the most recent arrests taking place in late June 2019.
Project Embrace collected evidence to suggest an Edmonton-based group coordinated the supply of drugs from British Columbia, and then facilitated distribution in Alberta – specifically in the communities of Bonnyville, Lloydminster, St. Paul, Cold Lake, Little Smoky and Frog Lake.
Investigators allege that Matthew Castle was at the centre of the Edmonton group, which involved family members and associates. Castle allegedly conspired with B.C.-based David Davinder Lally and Jacob Fralin to import drugs into Alberta.
Six homes were searched, including four in Edmonton and two Vancouver apartments. In total, investigators seized:
- 6.5 kilograms of cocaine;
- 2 kilograms of methamphetamine;
- 18 kilograms of a cocaine buffing agent;
- $342,982 cash; and
- a 2007 Volvo XC90 with a hidden mechanized compartment.
The following suspects were each charged with conspiracy to traffic drugs, in addition to a range of other offences:
- Matthew Castle, 29, from Edmonton;
- Terri Lynn Castle, 50, from Edmonton
- Christian Castle-Wasson, 18, from Edmonton;
- David Davinder Lally, 40, from Vancouver;
- Jacob Fralin, 32, from Vancouver; and
- Ryan Rautiainen, 26, from Lloydminster.
Project Embrace began in October 2018 when Bonnyville RCMP developed criminal intelligence about drug trafficking taking place in the area.
In conjunction with Project Embrace, Bonnyville RCMP arrested a number of street-level dealers in separate investigations. Each of the following was charged with multiple counts of drug trafficking:
- Charlie Houle, 24, from Bonnyville;
- Brent Coell, 18, from Bonnyville;
- Rayden Hill, 22, from Bonnyville;
- Michael Pownall, 36, from Bonnyville;
- Britney Coulombe, 27, from Bonnyville;
- Wayne Friesen, 27, from Bonnyville;
- Dustin Gellerman, 27, from Bonnyville.
A number of other police agencies were involved in Project Embrace, including Edmonton Police Service, Vancouver Police Department, RCMP K-Division, Kamloops RCMP, Lloydminster RCMP, Cold Lake RCMP, Elk Point RCMP, Kitscoty RCMP and St. Paul RCMP.
Members of the public who suspect drug or gang activity in their community can call local police, or contact Crime Stoppers at 1-800-222-TIPS (8477). Crime Stoppers is always anonymous.
ALERT was established and is funded by the Alberta Government and is a compilation of the province’s most sophisticated law enforcement resources committed to tackling serious and organized crime. Members of Calgary Police Service, Edmonton Police Service, Lethbridge Police Service, Medicine Hat Police Service, and RCMP work in ALERT.
Crime
The Left Thinks Drug Criminalization Is Racist. Minorities Disagree

[This article was originally published in City Journal, a public policy magazine and website published by the Manhattan Institute for Policy Research]
By Adam Zivo
A Canadian poll finds that racial minorities don’t believe drug enforcement is bigoted.
Is drug prohibition racist? Many left-wing institutions seem to think so. But their argument is historically illiterate—and it contradicts recent polling data, too, which show that minorities overwhelmingly reject that view.
Policies and laws are tools to establish order. Like any tool, they can be abused. The first drug laws in North America, dating back to the late nineteenth and early twentieth centuries, arguably fixated on opium as a legal pretext to harass Asian immigrants, for example. But no reasonable person would argue that laws against home invasion, murder, or theft are “racist” because they have been misapplied in past cases. Absent supporting evidence, leaping from “this tool is sometimes used in racist ways” to “this tool is essentially racist” is kindergarten-level reasoning.
Yet this is precisely what institutions and activist groups throughout the Western world have done. The Drug Policy Alliance, a U.S.-based organization, suggests that drug prohibition is rooted in “racism and fear.” Harm Reduction International, a British NGO, argues for legalization on the grounds that drug prohibition entrenches “racialized hierarchies, which were established under colonial control and continue to dominate today.” In Canada, where I live, the top public health official in British Columbia, our most drug-permissive province, released a pro-legalization report last summer claiming that prohibition is “based on a history of racism, white supremacy, paternalism, colonialism, classism and human rights violations.”
These claims ignore how drug prohibition has been and remains popular in many non-European societies. Sharia law has banned the use of mind-altering substances since the seventh century. When Indigenous leaders negotiated treaties with Canadian colonists in the late 1800s, they asked for “the exclusion of fire water (whiskey)” from their communities. That same century, China’s Qing Empire banned opium amid a national addiction crisis. “Opium is a poison, undermining our good customs and morality,” the Daoguang emperor wrote in an 1810 edict.
Today, Asian and Muslim jurisdictions impose much stiffer penalties on drug offenders than do Western nations. In countries like China, Saudi Arabia, Iran, Singapore, and Thailand, addicts and traffickers are given lengthy prison sentences or executed. Meantime, in Canada and the United States, de facto decriminalization has left urban cores littered with syringes and shrouded in clouds of meth.
The anti-drug backlash building in North America appears to be spearheaded by racial minorities. When Chesa Boudin, San Francisco’s former district attorney, was recalled in 2022, support for his ouster was highest among Asian voters. Last fall, 73 percent of Latinos backed California’s Proposition 36, which heightened penalties for drug crimes, while only 58 percent of white respondents did.
In Canada, the first signs of a parallel trend emerged during Vancouver’s 2022 municipal election, where an apparent surge in Chinese Canadian support helped install a slate of pro-police candidates. Then, in British Columbia’s provincial election last autumn, nonwhite voters strongly preferred the BC Conservatives, who campaigned on stricter drug laws. And in last month’s federal election, within both Vancouver and Toronto’s metropolitan areas, tough-on-crime conservatives received considerable support from South Asian communities.
These are all strong indicators that racial minorities do not, in fact, universally favor drug legalization. But their small population share means there is relatively little polling data to measure their preferences. Since only 7.6 percent of Americans are Asian, for example, a poll of 1,000 randomly selected people will yield an average of only 76 Asian respondents—too small a sample from which to draw meaningful conclusions. You can overcome this barrier by commissioning very large polls, but that’s expensive.
Nonetheless, last autumn, the Centre for Responsible Drug Policy (a nonprofit I founded and operate) did just that. In partnership with the Macdonald-Laurier Institute, we contracted Mainstreet Research to ask over 12,000 British Columbians: “Do you agree or disagree that criminalizing drugs is racist?”
The results undermine progressives’ assumptions. Only 26 percent of nonwhite respondents agreed (either strongly or weakly) that drug criminalization is racist, while over twice as many (56 percent) disagreed. The share of nonwhite respondents who strongly disagreed was three times larger than the share that strongly agreed (43.2 percent versus 14.3 percent). These results are fairly conclusive for this jurisdiction, given the poll’s sample size of 2,233 nonwhite respondents and a margin of error of 2 percent.
Notably, Indigenous respondents seemed to be the most anti-drug ethnic group: only 20 percent agreed (weakly or strongly) with the “criminalization is racist” narrative, while 61 percent disagreed. Once again, those who disagreed were much more vehement than those who agreed. With a sample size of 399 respondents, the margin of error here (5 percent) is too small to confound these dramatic results.
We saw similar outcomes for other minority groups, such as South Asians, Southeast Asians, Latinos, and blacks. While Middle Eastern respondents also seemed to follow this trend, the poll included too few of them to draw definitive conclusions. Only East Asians were divided on the issue, though a clear majority still disagreed that criminalization is racist.
As this poll was limited to British Columbian respondents, our findings cannot necessarily be assumed to hold throughout Canada and the United States. But since the province is arguably the most drug-permissive jurisdiction within the two countries, these results could represent the ceiling of pro-drug, anti-criminalization attitudes among minority communities.
Legalization proponents and their progressive allies take pride in being “anti-racist.” Our polling, however, suggests that they are not listening to the communities they profess to care about.
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
Invite your friends and earn rewards
Crime
National Health Care Fraud Takedown Results in 324 Defendants Charged in Connection with Over $14.6 Billion in Alleged Fraud
A 50-district dragnet uncovers transnational fraud, AI-driven deception, and systemic theft from Medicare, Medicaid, and U.S. taxpayers totaling over $14.6 billion
The Department of Justice announced Monday the outcome of the 2025 National Health Care Fraud Takedown, the largest coordinated enforcement action against health care fraud in U.S. history. Federal prosecutors have filed criminal charges against 324 individuals across 50 federal judicial districts and 12 State Attorneys General’s Offices, including 96 licensed medical professionals—among them doctors, nurse practitioners, and pharmacists. The defendants stand accused of orchestrating fraudulent schemes amounting to more than $14.6 billion in intended losses to Medicare, Medicaid, and other federally funded programs.

This historic enforcement action more than doubles the previous national record of $6 billion. As part of this effort, federal and state authorities have seized over $245 million in cash, luxury vehicles, cryptocurrency, and other high-value assets. The Centers for Medicare & Medicaid Services (CMS) separately reported that it successfully prevented more than $4 billion in fraudulent payments in the months leading up to the Takedown. CMS also confirmed that it suspended or revoked the billing privileges of 205 providers linked to fraudulent activity. In the civil domain, federal agencies filed actions against 20 defendants tied to $14.2 million in alleged fraud and finalized civil settlements with an additional 106 defendants, totaling $34.3 million in recovered funds.
The Takedown was led by the Health Care Fraud Unit of the DOJ Criminal Division’s Fraud Section and carried out in close coordination with U.S. Attorneys’ Offices nationwide, the Department of Health and Human Services Office of Inspector General (HHS-OIG), the Federal Bureau of Investigation (FBI), the Drug Enforcement Administration (DEA), and multiple state law enforcement agencies. Medicaid Fraud Control Units in 18 states also played a central role in investigating and prosecuting the cases.
In remarks accompanying the announcement, Secretary of Health and Human Services Robert F. Kennedy Jr. emphasized that the agency would aggressively work with law enforcement to eliminate the “pervasive health care fraud that drove up costs and harmed patients under the former administration.” Attorney General Pamela Bondi echoed the urgency, calling the action “justice delivered to those who steal from taxpayers and endanger lives.” Matthew R. Galeotti, head of the Justice Department’s Criminal Division, underscored the gravity of the crimes targeted, noting that fraudulent schemes often lead not only to financial losses but also to direct patient harm, including medically unnecessary procedures and worsened addiction outcomes.
FBI Director Kash Patel emphasized that this Takedown represents the largest in the bureau’s history, highlighting the theft of more than $13 billion from federal health programs. Acting Inspector General Juliet T. Hodgkins of HHS-OIG described the scale of harm as unprecedented and reaffirmed the agency’s commitment to safeguarding the public.
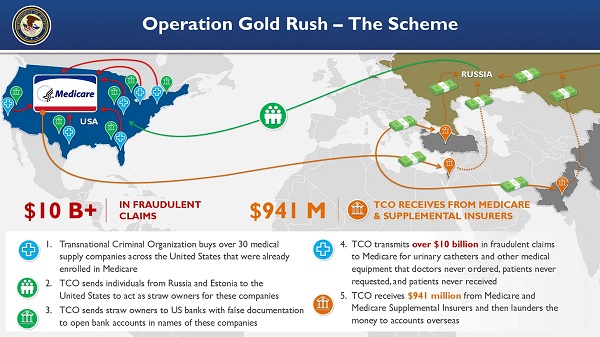
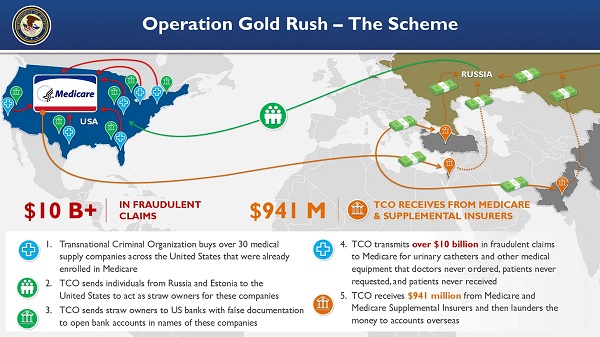
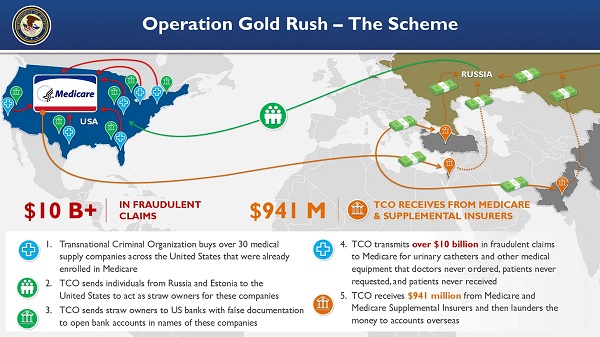
Among the most significant components of this national operation was Operation Gold Rush, which uncovered a sophisticated transnational conspiracy responsible for over $10 billion in fraudulent Medicare claims. The scheme was orchestrated by foreign nationals who, acting as a coordinated criminal enterprise, acquired more than 30 medical supply companies across the United States. These companies had already been enrolled in Medicare, and were then used to funnel false claims for urinary catheters and other durable medical equipment. Stolen identities of over one million Americans were used to submit these claims, which had not been requested by patients, nor ordered by physicians.
The conspiracy relied on straw owners sent from Russia and Estonia to the U.S., who were directed by co-conspirators communicating through encrypted channels. Using fraudulent documentation, these straw owners opened U.S. bank accounts for laundering proceeds. Though the organization submitted over $10.6 billion in claims, CMS successfully blocked most of the payments. Only approximately $41 million reached the conspirators via Medicare, but approximately $900 million was disbursed by Medicare supplemental insurers before the fraud was detected.
Four individuals were arrested in Estonia and eight others were apprehended at major U.S. airports and border crossings as they attempted to flee. Law enforcement seized approximately $27.7 million in fraud proceeds from this operation.

Federal prosecutors filed related charges in five districts: the Central District of California, the Middle District of Florida, the Northern District of Illinois, the District of New Jersey, and the Eastern District of New York.
In a separate scheme centered in Illinois, the Department brought charges against five individuals, including two executives from Pakistani marketing firms, who used artificial intelligence to generate fake audio recordings of Medicare beneficiaries purporting to consent to receive medical equipment. This fraudulent data was sold to laboratories and equipment suppliers, which used it to file $703 million in false claims. Approximately $418 million was ultimately paid out on these claims, and the government has so far seized $44.7 million in related assets. The fraud involved not only AI-based deception but also the illegal sale and laundering of stolen personal health information.
Another case exposed a billing company executive based in Pakistan and the United Arab Emirates who conspired with addiction treatment centers to submit approximately $650 million in fraudulent claims to Arizona Medicaid. Some services billed were never rendered, and others were so deficient as to provide no therapeutic value. The operation targeted vulnerable individuals, including members of Native American tribes and the homeless. Kickbacks were paid for patient referrals, and the executive used at least $25 million in illicit funds to purchase a $2.9 million home in Dubai.

The Department also charged 49 defendants in connection with over $1.17 billion in fraudulent claims tied to telemedicine and genetic testing. In one Florida case, an owner of both telemedicine and durable medical equipment companies orchestrated a $46 million scheme involving deceptive telemarketing campaigns that generated unauthorized genetic testing and equipment claims. The Department continues to prioritize cases involving telehealth-based fraud, which often exploits unwitting patients through misrepresented or manufactured consent.
Prescription opioid diversion was another central focus of the Takedown. A total of 74 defendants, including 44 licensed medical professionals, were charged across 58 criminal cases for illegally distributing more than 15 million opioid pills. One Texas pharmacy alone was responsible for over 3 million of these pills, which included highly addictive substances such as oxycodone, hydrocodone, and carisoprodol. The DEA concurrently announced 93 administrative actions to revoke licenses and registrations of pharmacies and providers implicated in the unlawful handling of controlled substances.
Other cases include a $28.7 million scheme in Tennessee involving medications falsely billed to the Federal Employees’ Compensation Fund, where prescriptions were neither authorized by physicians nor dispensed as claimed. In separate indictments filed in Washington and California, medical providers were charged with stealing fentanyl and hydrocodone intended for pediatric patients under anesthesia.
The geographic scope of the Takedown was vast. In total, 189 federal cases were filed across all 50 federal judicial districts, and 91 state-level cases were brought in 12 states by participating Attorneys General. This unprecedented coordination underscores the national impact and bipartisan support for rooting out fraud in American health care systems.
To enhance ongoing efforts, the Department also announced the establishment of a new Health Care Fraud Data Fusion Center.

This joint initiative brings together specialists from the DOJ’s Health Care Fraud Unit, HHS-OIG, FBI, and CMS to leverage cloud computing, artificial intelligence, and large-scale data analytics to detect emergent fraud patterns. The Fusion Center aligns with Executive Order 14243, “Stopping Waste, Fraud, and Abuse by Eliminating Information Silos,” which mandates interagency cooperation and data-sharing to reduce redundancy and increase efficiency in enforcement.
Principal Assistant Deputy Chief Jacob Foster, Assistant Deputy Chief Rebecca Yuan, Trial Attorney Miriam L. Glaser Dauermann, and Data Analyst Elizabeth Nolte coordinated this year’s Takedown from within the DOJ’s Health Care Fraud Unit. Prosecutors from the National Rapid Response team and regional Strike Forces in 27 districts led casework alongside U.S. Attorneys’ Offices and 18 state Medicaid Fraud Control Units. Additional support came from the Department of Labor, VA-OIG, IRS Criminal Investigation, Homeland Security Investigations, the Defense Criminal Investigative Service, the Office of Personnel Management, the United States Postal Service OIG, and numerous other federal and local agencies.
Image sources: US DOJ
-

 Alberta7 hours ago
Alberta7 hours agoAlberta Independence Seekers Take First Step: Citizen Initiative Application Approved, Notice of Initiative Petition Issued
-
 Crime6 hours ago
Crime6 hours agoNational Health Care Fraud Takedown Results in 324 Defendants Charged in Connection with Over $14.6 Billion in Alleged Fraud
-

 Health5 hours ago
Health5 hours agoRFK Jr. Unloads Disturbing Vaccine Secrets on Tucker—And Surprises Everyone on Trump
-

 Bruce Dowbiggin8 hours ago
Bruce Dowbiggin8 hours agoThe Game That Let Canadians Forgive The Liberals — Again
-

 Alberta1 day ago
Alberta1 day agoCOVID mandates protester in Canada released on bail after over 2 years in jail
-

 Alberta2 days ago
Alberta2 days agoAlberta uncorks new rules for liquor and cannabis
-

 armed forces1 day ago
armed forces1 day agoCanada’s Military Can’t Be Fixed With Cash Alone
-

 Crime2 days ago
Crime2 days agoProject Sleeping Giant: Inside the Chinese Mercantile Machine Linking Beijing’s Underground Banks and the Sinaloa Cartel







 By
By 



