Crime
Update: RCMP continue to seek public assistance to find murder suspects

Jan. 2, 2020
RCMP Major Crimes Unit seeking assistance to locate two subjects wanted on warrant –Update #2
Cochrane, Alta. – The RCMP Major Crimes Unit continues to seek the public’s assistance in locating Trista Nadene Tinkler, Robert Gordon Daignault and the stolen 2013 Kia Optima. It is believed the suspects may be in the Edmonton area; however, the location of the vehicle remains unknown.
Tinkler is described as: 5 feet 6 inches, 154 lbs with red hair and brown eyes.
Daignault is described as: 5 feet 9 inches, 185 lbs with hazel eyes and a bald head.
The vehicle is described as a 2013 Kia Optima, Bronze in colour, with Alberta license plate E22149.
The RCMP believe that these two individuals may be armed and present a danger to the public. If you see them or know their whereabouts, or locate the vehicle, please contact the Cochrane RCMP at 403-851-8000, or call your local police agency. If you wish to remain anonymous, you can contact Crime Stoppers at 1-800-222-8477 (TIPS), online at www.P3Tips.com or by using the “P3 Tips” app available through the Apple App or Google Play Store.
December 31, 2019
RCMP Major Crimes Unit seeking assistance to locate two subjects wanted on warrant
Cochrane, Alta. – The RCMP Major Crimes Unit has obtained arrest warrants for two adults who are believed to be in possession of a stolen vehicle related to an earlier death investigation.
On December 29, 2019 the Major Crimes Unit took carriage of an investigation into a male found deceased near Spring Bank Airport. Today, an autopsy was completed and the manner of death was determined to be a homicide.
The victim’s car has not been recovered by the RCMP, and arrest warrants have been obtained for two subjects believed to be in possession of the vehicle. Public assistance is being sought to locate these two subjects and the vehicle. They may be in the Calgary area.
Trista Nadene TINKLER a 34-year-old female has been charged with:
- Possession of property obtained by crime – Section 354 of the Criminal Code
- Theft of Credit Card – Section 342(1)(a) of the Criminal Code
- Failure to comply with Appearance Notice or Promise to Appear – Section 145(5)(A) of the Criminal Code.

Trista Nadene Tinkler
TINKLER is described as: 5 feet 6 inches, 154 lbs with red hair and brown eyes.
Robert Gordon DAIGNAULT a 51-year-old male has been charged with:
- Possession of property obtained by crime – Section 354 of the Criminal Code
- Theft of Credit Card – Section 342(1)(a) of the Criminal Code
- Failure to comply with Appearance Notice or Promise to Appear – Section 145(5)(A) of the Criminal Code.
- Resisting or Obstructing a Peace Officer – Section 129(A) of the Criminal Code

Robert Gordon DAIGNAULT
DAIGNAULT is described as: 5 feet 9 inches, 185 lbs with hazel eyes and a bald head.
The vehicle is described as a 2013 Kia Optima, Bronze in colour, with Alberta license plate E22149.

The RCMP believe that these two individuals may be armed and present a danger to the public. If you see them or know their whereabouts, or you locate the vehicle, please contact the Cochrane RCMP at 403-851-8000, or call your local police agency. If you wish to remain anonymous, you can contact Crime Stoppers at 1-800-222-8477 (TIPS), online at www.P3Tips.com or by using the “P3 Tips” app available through the Apple App or Google Play Store.
No further information is available at this time in relation to the nature of these charges.
BACKGROUND:
Dec. 29, 2019
RCMP Major Crimes Unit investigating suspicious death
Cochrane, Alta. – At 8:30 a.m. today, Cochrane RCMP responded to a report of a deceased male located off of a rural road near the Spring Bank Airport. Responding RCMP determined that the death is suspicious and the Major Crimes Unit South has taken carriage of the investigation.
RCMP members including the Forensic Identification Section remain on scene to conduct an examination.
An autopsy of the male is scheduled for Dec. 31. Investigators are working to confirm the identity of the adult male.
No further information is available. The RCMP will provide an update following the autopsy.
Crime
DEA Busts Canadian Narco Whose Chinese Supplier Promised to Ship 100 Kilos of Fentanyl Precursors per Month From Vancouver to Los Angeles
A Hollywood-style DEA sting revealed a seamless pipeline from Vancouver brokers to Los Angeles cartel operatives and Australian drug markets.
A senior Indo-Canadian gangster from an ultra-violent British Columbia–based fentanyl trafficking gang with ties to Latin cartels, Chinese Triads, and Hezbollah was taken down in a stunning U.S. government sting that saw a thick-accented Chinese narco casually promise an undercover agent at a Vancouver café that he could ship 100 kilograms of fentanyl precursors per month from Vancouver to Los Angeles, using his trucking company fronted by an Indo-Canadian associate.
The case is detailed in a sprawling DEA probe spanning Turkey, Mexico City, Dubai, Australia, Toronto, Vancouver, Montreal, Hong Kong, and Los Angeles — all captured in a 29-page affidavit with scenes so surreal they could rival a Hollywood script, complete with underworld nicknames like “Burger,” “Queen,” and “Darth Vader.”
At the center is Opinder Singh Sian, a Canadian national and longtime Lower Mainland underworld figure who survived targeted shootings and reportedly leads the Brothers Keepers gang — a key proxy for the Sinaloa cartel in Canada, interoperable with other Latin American cartels, Chinese Communist Party chemical suppliers, and working alongside the Kinahans, a notorious Irish crime family now based in Dubai and closely linked to Hezbollah finance networks.
Sian has been arrested in Arizona and indicted in a sweeping U.S. case that underscores British Columbia’s critical role as a global trafficking hub, bringing together Mexican cartels and Chinese precursor suppliers that operate with near impunity in Vancouver but are increasingly the focus of elite U.S. law enforcement.
The affidavit illustrates how Vancouver’s criminal networks have funneled Chinese precursors into the United States and directly tied them to methamphetamine deals with Mexican gangsters on Los Angeles streets — part of one of the most sophisticated narcotics smuggling conspiracies ever uncovered in North America.
The explosive details are laid out in a newly unsealed affidavit filed by U.S. federal agent Albert Polito in support of a criminal complaint and arrest warrant against Sian. Sworn in 2024, the document offers a rare inside look at how Vancouver’s street-level crews transformed into global brokers bridging continents and more sophisticated criminal syndicates.
Much of the case focuses on methamphetamine shipments from Los Angeles to Australia, orchestrated by Sian, who acted as a proxy for more senior transnational Mexican, Chinese, and Iranian networks, experts say.
“Local gangs like Brothers Keepers aren’t just street crews — they’re frontline proxies in transnational narcoterror networks,” former Canadian intelligence analyst Scott McGregor, an expert on the nexus of Chinese and Iranian threats and foreign interference, commented on X. “Ignoring them as low-level threats misses their role in laundering, logistics, and hybrid warfare.”
But the penultimate finding — likely of high interest in Washington political circles — came from a stunning investigative meeting. In August 2023, the DEA affidavit describes how a shadowy U.S. undercover source known as “Queen” or CS-1 sat across from a man in Vancouver speaking with a thick Chinese accent.
The man, later identified as Peter Peng Zhou, explained in detail how he could “receive fentanyl precursor chemicals from China into Vancouver” and “send 100 kilos of chemicals per month to Los Angeles” using his British Columbia trucking company run by an Indo-Canadian associate.
Zhou allegedly told CS-1 that he had been doing this for about ten years and remembered when these kilograms of chemicals were upwards of $300,000 each. He claimed he knew how to make fentanyl and methamphetamine from the chemicals and emphasized that he would require upfront payment before sending any shipments south to Los Angeles.
Demonstrating how casually Vancouver’s narcos blend into upscale environments, the affidavit describes how Sian first dined at a downtown restaurant with his wife, child, and CS-1 before taking “The Queen” to meet his precursor suppliers at a coffee house.
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
That critical meeting, involving Sian, Zhou, and other associates, provided prosecutors with some of the clearest evidence yet of a direct chemical pipeline from Chinese suppliers into North American distribution networks, routed first through Vancouver’s port and trucking infrastructure.
The investigation began in June 2022 when DEA agents in Ankara, Turkey, received intelligence about an opportunity to embed a confidential source into a global trafficking organization. This network needed help moving large shipments of methamphetamine and cocaine from Southern California to Australia — one of the world’s most lucrative drug markets.
DEA agents provided their Ankara counterparts with the phone number of CS-1 — known in global gang networks as “Queen” — who posed as an international logistics coordinator. A Turkish narco, Ibrahim Ozcelik, made initial contact and then passed CS-1’s details to a North American leader: Opinder Singh Sian.
After initial communications, Sian and CS-1 arranged an in-person meeting in Vancouver on February 1, 2023. During this pivotal encounter, Sian claimed to work closely with Irish organized crime — specifically the Kinahan family — as well as Italian groups and other powerful Canadian gangs. Outside Canada, he described sourcing drugs directly from major Mexican and South American cartels, reinforcing his role as a cross-border broker capable of linking multiple criminal networks. He also said he collaborated with a known Turkish drug kingpin, Hakan Arif, highlighting the global scope of his alliances.
While in Vancouver, Sian introduced CS-1 to two male associates. They explained they had about 500 kilograms of cocaine stockpiled and needed help moving it through Los Angeles ports and on to Australia. CS-1 claimed they could facilitate offloading in Los Angeles, repackaging, and onward shipping via container vessel — a scheme designed to tap into Australia’s sky-high wholesale prices, which exceed $200,000 per kilogram.
In March 2023, Sian and CS-1 met again at a restaurant in Manhattan Beach, California, to discuss expanding into methamphetamine smuggling. “Queen” also brought along a DEA undercover agent (“UC-1”), posing as a cousin who worked at the Port of Long Beach and helped move narcotics undetected.
At the meeting, Sian expressed caution, acknowledging they could get in trouble just for meeting. He said his first shipment would be “200,” consistent with earlier encrypted text conversations. UC-1 advised doing fewer but larger shipments to reduce detection risk, emphasizing this was only done for CS-1 as “family.”
Sian pressed for details about the port, probed UC-1’s connections, and mentioned knowing other contacts at the port, the DEA alleges.
By June 2023, the plan to move large methamphetamine shipments into the U.S. began to accelerate. Sian advised that he and his associates would deliver an estimated 500 to 750 kilograms of methamphetamine in separate drops coordinated by his network. On June 13, 2023, Sian created an encrypted chat group using the alias “Cain,” adding “Sticks” (later identified as Sebastian Rollin, a Canadian based in Montreal) and CS-1.
Rollin allegedlly informed CS-1 that his crew would soon deliver 30 pounds of methamphetamine in Southern California as part of the first staged shipment.
Another trafficker known as “El R” or “The R,” later identified as Ruben Chavez Ibarra, entered the operation.
The DEA’s Los Angeles operation revealed gritty street-level deals directly tying Sian’s Indo-Canadian group to “Queen’s” Mexican networks. On July 6, 2023, after days of negotiation, Jorge Orozco-Santana arranged a pick-up in Anaheim using a white Mercedes. He verified the deal with the serial number of a dollar bill token, handed over two plastic bins containing 84.6 kilograms of methamphetamine. The DEA tied this deal to the Montreal network involved in Sian’s encrypted chats.
On July 29, 2023, Sian created a new Threema group chat including a new associate using the moniker “AAA,” later identified as Tien Vai Ty Truong — a dual citizen of Vietnam and Canada, with narco operations in Toronto and Vancouver directed from Hong Kong, according to the DEA affidavit.
The group discussed the 30-pound and 200-pound loads and planned their shipment to Australia. On August 1, Sian asked CS-1 to call an associate named Kular to manage mounting anxiety among Mexican sources over shipment delays.
Meanwhile, CS-1 began discussing fentanyl precursor chemicals with Kular and Sian.
This line of discussion began because Kular had first asked CS-1 whether her networks could receive direct ketamine shipments into Mexico City — a question that suggested to the DEA that Sian’s network likely had direct access to Chinese Communist Party–linked drug suppliers and large-scale chemical manufacturing channels.
In response, the DEA’s High Intensity Drug Trafficking Area Group 48 team prompted “Queen” to pivot and ask about fentanyl precursors. Queen did so, requesting prices on two critical compounds: 1-BOC-4-piperidone and 1-BOC-4-anilinopiperidine. Kular replied that the price would be $225 for the first chemical and $750 for the second, plus $1,000 for shipping.
Shortly after, on July 25, 2023, Sian himself directly contacted Queen, claiming he could supply those same precursors directly and even provide initial samples. He said he could get the chemicals “straight from China,” and proposed shipping them by container into the Port of Long Beach.
To build trust, Sian offered to mail a sample first. On July 29, Queen provided Sian with an undercover DEA-controlled PO box. That same day, Sian confirmed he had sent 20 grams of 1-BOC-4-piperidone and said he would accept cryptocurrency (specifically USDT, also known as Tether) for future large orders. By August 10, Sian informed Queen that the sample shipment had been sent, though it might not arrive until the following week — further confirming the group’s operational capacity to source Chinese precursors and move them into the U.S.
This was the evidence the DEA needed to take the Vancouver port fentanyl sting into high gear.
Returning to Vancouver in August, the headline-making fentanyl meeting came into full context. On August 16, 2023, CS-1 met Sian and his wife and child for lunch in downtown Vancouver. After lunch, Sian drove CS-1 to meet two individuals capable of sending bulk fentanyl precursor chemicals into the United States.
At a coffee shop, Peter Peng Zhou — speaking with a heavy Chinese accent — described how he could receive precursor shipments from China into Vancouver and move 100 kilograms per month to Los Angeles using his British Columbia trucking company.
In an almost absurdly candid aside, Zhou introduced his partner, known as “Burger,” described as a Southeast Asian male who managed “the money side” of the business for him. According to the DEA affidavit, Burger bluntly said he was involved because “his wife was very greedy and wanted him to make more money.”
The pivotal Vancouver coffee meeting also brought in more connections to Mexican operatives in California. During the same meeting, Sian mentioned a contact named Orlando, referring to Orlando Escutia, a Bakersfield, California–based associate. Sian explained that Escutia would be delivering CS-1 an additional 50 kilograms of methamphetamine the following week for shipment to Australia.
Zhou further revealed he could start acquiring a new fentanyl precursor with a CAS number ending in 228, describing it as a “newer and better” chemical for making fentanyl. He elaborated that when he shipped these chemicals by mail, he used a special bag designed to evade law enforcement detection, the DEA alleges.
Later that same day, CS-1 and Sian met with another key figure known as “ABC,” later identified as Kular, at a restaurant in downtown Vancouver. Kular claimed that his own boss, “AAA” — later identified as Tien Truong — was a Chinese national about 55 years old, mainly operating in the Toronto area. According to Kular, Truong’s bosses were ultimately based out of Hong Kong and specialized in moving large quantities of cocaine and methamphetamine around the world.
Crime
‘We’re Going To Lose’: Steve Bannon Warns Withholding Epstein Files Would Doom GOP

From the Daily Caller News Foundation
By Jason Cohen
Former White House adviser Steve Bannon warned on Friday that Republicans would suffer major losses if President Donald Trump’s administration does not move to release documents related to deceased pedophile Jeffrey Epstein’s crimes and associations.
Axios reported on Sunday that a two-page memo showed the Department Of Justice (DOJ) and FBI found no evidence Epstein kept a “client list” or was murdered, but public doubts have continued. Bannon said on “Bannon’s War Room” that failure to release information would lead to the dissipation of one-tenth of the Make America Great Again (MAGA) movement and significant losses for the Republican Party in the 2026 midterms and the 2028 presidential election.
Dear Readers:
As a nonprofit, we are dependent on the generosity of our readers.
Please consider making a small donation of any amount here.
Thank you!
“It’s not about just a pedophile ring and all that, it’s about who governs us, right? And that’s why it’s not going to go away … For this to go away, you’re going to lose 10% of the MAGA movement,” Bannon said. “If we lose 10% of the MAGA movement right now, we’re going to lose 40 seats in ’26, we’re going to lose the [presidency]. They don’t even have to steal it, which they’re going to try to do in ’28, because they’re going to sit there and they go, ‘They’ve disheartened the hardest-core populist nationalists’ — that’s always been who governs us.”
Bannon also demanded the publication of all the Epstein documents on “Bannon’s War Room” Thursday. He called on the DOJ to go to court and push for the release of the documents or for Trump to appoint a special counsel to manage the publication.
Epstein was arrested in 2019 and charged with sex trafficking. Shortly after, he was found dead in his New York Metropolitan Correctional Center cell shortly after. Officials asserted that he hanged himself in his cell.
However, Epstein’s death has sparked years of theories because of the malfunctioning of prison cameras, along with guards admitting to falsifying documents about checking on the then-inmate. The DOJ inspector general later confirmed that multiple surveillance cameras outside of his cell were inoperable, while others captured the common area outside his door.
Both Bannon and Daily Caller News Foundation co-founder Tucker Carlson have speculated that Epstein had connections to intelligence agencies.
Former Labor Secretary Alex Acosta allegedly indicated that Epstein was tied to intelligence, according to Vicky Ward in The Daily Beast.
-

 Addictions1 day ago
Addictions1 day agoWhy B.C.’s new witnessed dosing guidelines are built to fail
-

 Frontier Centre for Public Policy2 days ago
Frontier Centre for Public Policy2 days agoCanada’s New Border Bill Spies On You, Not The Bad Guys
-
 Business1 day ago
Business1 day agoCarney Liberals quietly award Pfizer, Moderna nearly $400 million for new COVID shot contracts
-

 Energy2 days ago
Energy2 days agoCNN’s Shock Climate Polling Data Reinforces Trump’s Energy Agenda
-

 Opinion1 day ago
Opinion1 day agoCharity Campaigns vs. Charity Donations
-

 Business1 day ago
Business1 day agoMark Carney’s Fiscal Fantasy Will Bankrupt Canada
-
 Opinion1 day ago
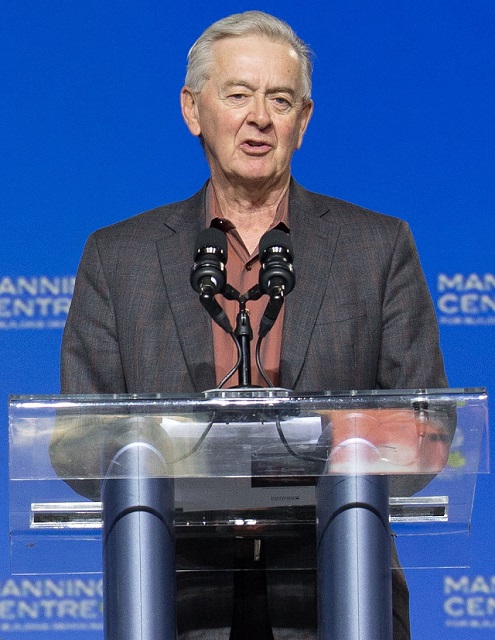
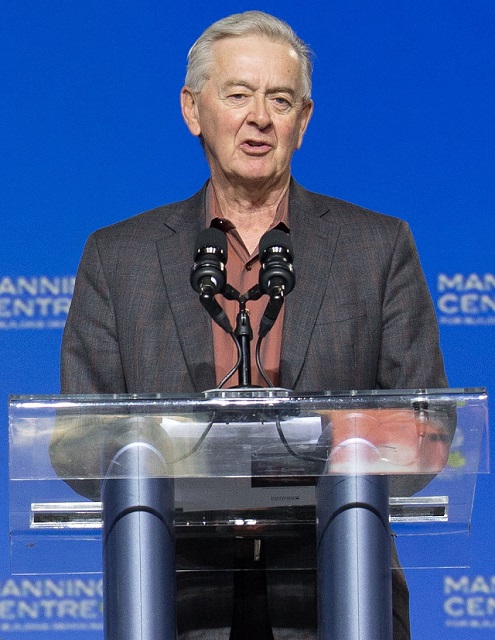
Opinion1 day agoPreston Manning: Three Wise Men from the East, Again
-

 Red Deer1 day ago
Red Deer1 day agoWesterner Days Attraction pass and New Experiences!








