Crime
Red Deer RCMP arrest man in two stolen vehicles over one and a half days

Red Deer, Alberta – A Red Deer man appears in court today after RCMP arrested him in two different stolen vehicles within the space of a day and a half. In court, he will also speak to a theft file from the summer in the downtown, in which he was arrested during the commission of a theft by the Red Deer RCMP Crime Reduction Team and then later arrested again in the December warrant round-up.
Shortly before 8 pm on January 28, RCMP located the suspect in a stolen vehicle parked in a busy north Red Deer lot, thanks to a tip from the public. RCMP blocked the vehicle in to prevent it fleeing and endangering pedestrians and drivers in the parking lot; the male suspect got out of the vehicle and was arrested without incident. RCMP seized methamphetamine from the suspect during his arrest. The vehicle had been stolen that morning out of Red Deer when it was left running and unlocked.
Brandon Loughlin was released on January 29 on a $2,500 no cash recognizance to appear in court on February 2. A condition of his release was that he was banned from being in any vehicle without the registered owner present
At 6 am on January 30, Red Deer RCMP responded to a report of a vehicle that had been stolen when it was left running and unlocked. RCMP located the vehicle with support from OnStar, and had OnStar shut the vehicle down slowly at a location where police determined there would be no danger to other drivers or pedestrians. Once the vehicle was stopped, the suspect, identified as Brandon Loughlin, attempted to flee on foot but was arrested after a brief foot chase.
Brandon Loughlin was then remanded to appear in court in Red Deer on both stolen vehicle files on February 1 at 9:30 am.
During his court appearance today, Loughlin will also speak to charges on a file from June 30, 2017, where he was arrested in downtown Red Deer after a member of the Red Deer RCMP crime reduction team on patrol in the downtown observed him stealing a bicycle and arrested him. Loughlin failed to appear in court on that file and a warrant was issued for his arrest; the warrant was executed by Red Deer RCMP during the warrant round-up in December, and Loughlin made his first court appearance on the theft of bicycle file on January 11.
20 year old Brandon Robert Loughlin faces the following charges with relation to all the above-noted files:
· Criminal Code 355(a) – Possession of stolen property over $5,000 X 2
· Criminal Code 334(b) – Theft under $5,000
· Criminal Code 145(3) – Fail to comply with conditions
· Criminal Code 145(5) – Fail to comply with conditions
· Criminal Code 430(4) – Mischief under $5,000
· CDSA 4(1) – Possession of Schedule I substance (methamphetamine)
“This series of incidents demonstrates the importance of our Pinpoint crime reduction strategies and their focus on prolific offenders. It also highlights our commitment to public safety and the importance of community engagement,” says Inspector Gerald Grobmeier of the Red Deer RCMP. “This suspect was arrested thanks to crime reduction strategies like our downtown patrols, and our successful warrant round-ups. During both stolen vehicle arrests, RCMP employed strategies to minimize potential harm to the public, and one of the arrests was thanks to a vigilant citizen who recognized the stolen vehicle from a social media page. A successful approach to crime reduction involves a lot of complex elements, and I’m pleased to see how many were used to maximum effect in this series of files.”
RCMP remind citizens that criminals prowl neighbourhoods and business parking lots across the city looking for easy theft opportunities. While police recognize that vehicles need to warm up in the winter months, they advise that vehicles should not be left unattended, that they always be locked and without valuables left inside, and that citizens consider investing in theft prevention devices
Crime
Project Sleeping Giant: Inside the Chinese Mercantile Machine Linking Beijing’s Underground Banks and the Sinaloa Cartel

U.S. surveillance image shows one of Sai Zhang’s top lieutenants crossing into Mexico with a money courier for the Sinaloa cartel. The photo revealed critical ties between Zhang’s transnational money laundering and drug trafficking operation and one of North America’s dominant fentanyl distributors.
 Sam Cooper
Sam Cooper
Former senior DEA official describes covert global financial ecosystem tying Chinese students, Sinaloa fentanyl sales, cartel cash collection, and PRC state-linked infrastructure deals.
In January 2021, a grainy black-and-white surveillance photo quietly accelerated one of the most consequential geopolitical investigations in recent times — a case with influence over border security, trade policy, and tariff disputes shaping our era.
Captured at the U.S.-Mexico border, the image showed a thick-set Chinese man wearing a COVID-era face mask driving alongside a Mexican man — a key money launderer for the Sinaloa cartel. The Chinese man turned out to be a senior operative working for Sai Zhang, a younger Chinese international student living in the United States on a student visa.
To a small group of U.S. federal agents, the photo revealed a thread they had been painstakingly unraveling since 2018, part of an ongoing investigation known as Project Sleeping Giant.
The overarching task force, launched by senior DEA agent Don Im — whose career was built on decoding China’s paramount role in global money laundering and supply of chemicals used to produce methamphetamine and fentanyl — aimed to bring cases against Latin cartels working with Chinese money launderers.
This photo was the first concrete step toward proving a direct, operational bridge between Chinese underground banking networks and the blood-soaked heart of Mexico’s most notorious cartel.
While evidence of Sai Zhang’s commanding role in orchestrating Sinaloa fentanyl cash flows was stunning, the involvement of Chinese student networks followed its own curious logic, Im explained in an interview.
“Chinese banking networks were operating in the U.S. long before Zhang linked up with the Sinaloa cartel,” Im said, describing the system in which Chinese buyers bid on pools of drug cash collected in cities worldwide, paying a premium to receive laundered dollars in American locations and investments of their choosing. “The buyers were mostly wealthy Chinese seeking dollars for real estate or tuition in America. Payments were made in yuan through Chinese accounts. In return, Mexican cartels received goods or cash.”
In exclusive interviews, Im revealed in unprecedented details the breathtaking complexity of China’s global drug money laundering networks — a system of Byzantine paths that Sleeping Giant helped map and penetrate. The troubling implications help explain why Washington is now imposing trade sanctions targeting China and countries deeply entwined with its export-driven economy.
At the heart of it, Beijing’s centralized economic apparatus and the Chinese Communist Party’s regional governors knowingly align with global drug barons — channeling fentanyl cash, reintegrating it into China’s factory output, and exporting drug-funded “legitimate” goods worldwide. Meanwhile, Chinese immigrants and travelers access the other side of this narco-banking system, using it to bankroll overseas investments and strengthen the reach of the Chinese diaspora.
It is a system that works for China’s government and citizens alike — on the micro level, it pays for tuition and housing for Chinese students in America; on the macro level, it helps fund Xi Jinping’s Belt and Road infrastructure projects abroad, designed to bind other states more closely to China through trade, debt, and ultimately elite corruption. According to Im, the chemical precursors fueling the production of fentanyl, methamphetamine, and ecstasy in parts of Europe — as well as in countries like Canada and Mexico — are woven into this Belt and Road system.
“Their Belt and Road Initiative is now in over a hundred-and-some-odd countries — with ports, airports, shipping lanes, roads, highways, trains. And all of China’s precursor chemicals are being offloaded,” Im said. “Right now, China’s economy is in dire straits, and they’re looking for capital to pay off debt, fund projects, make investments, or transfer wealth out of China. And that’s huge business. It involves provincial authorities engaged in various organized crime activities, including bribery, intimidation, kickbacks, and providing tariff breaks to known illicit drug and chemical suppliers.”
Don Im has testified on these findings before Congress, and related U.S. government investigations have shown that Beijing provides tax incentives to fentanyl factories.
As Sleeping Giant revealed, a critical cog in Beijing’s Trojan horse system is the Chinese student visitor — exemplified by figures like Sai Zhang.
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
The Student Banker
Sai Zhang arrived in the United States on a student visa. By the late 2010s, he had quietly transformed himself into a key broker in a vast underground banking network centered in Southern California. His customers were wealthy Chinese nationals circumventing Beijing’s strict $50,000 annual foreign exchange cap.
Zhang’s operation was deceptively elegant. He tapped into the surplus of U.S. dollars held by Mexican drug cartels from opioid-ravaged eastern states such as North Carolina to cartel-influenced streets in Los Angeles. The Sinaloa drug barons, flush with cash from fentanyl, meth, and cocaine sales, needed a discreet and cost-effective way to convert their U.S. dollar profits back into pesos in Mexico.
Zhang’s network — as is true for all Chinese money brokers — clipped both sides of the ticket, offering direct or indirect services to Mexican cartels, Chinese factory producers, Chinese diaspora retailers across Europe and the western hemisphere who sell Chinese goods, and Chinese citizens seeking to import their yuan-denominated wealth, receiving non-traditional banking payouts in American cities.
So Zhang bought the Sinaloa cartel’s fentanyl cash dollars at a discount, resold them at a premium to Chinese buyers, and closed a loop that turned violent, street-level drug cash into fuel for China’s GDP.
But for U.S. prosecutors working alongside DEA street teams, what had long been known by detectives since the landmark case of Mexican-Chinese methamphetamine baron Zhenli Ye Gon—that is, the deep integration between Chinese and Mexican narco networks—still had to be painstakingly proven in court.
For Sai Zhang, this meant cutting through a labyrinth of protective layers carefully constructed to shield elite money brokers from exposure.
As described in voluminous U.S. court records—and corroborated in detail by Don Im—Zhang relied on a sophisticated chain of cash couriers, brokers, and money mules to keep himself insulated from street-level narcotics transactions. DEA surveillance teams tracked network operators to numerous cash stash houses and clandestine parking lot exchanges, often coming tantalizingly close yet narrowly missing opportunities to link Zhang’s cash directly to drug shipments.
One example is detailed in the affidavit of lead investigator Steven Gonzales. Surveillance teams tracked Xuanyi Mu and Hang Su from the “Naomi Avenue” stash house in Arcadia to a parking lot, where they met Elizabeth Sevilla-Mendoza, a known narcotics courier. Su collected an orange tote bag from her before returning to her black Mercedes-Benz. Officers then directed a traffic stop and deployed a K-9 unit, which alerted to the scent of narcotics on the bag. Inside, agents discovered $34,000 in foil-wrapped cash, neatly stacked and bound with rubber bands.
But within 48 hours of seizing this cash, Zhang’s team shut down the Arcadia stash house, leaving DEA investigators without the drug seizure they needed and cutting off a valuable surveillance node.
The first major break came on October 18, 2022. Acting on a tip from DEA agents in Charlotte, North Carolina, investigators in California zeroed in on a supermarket parking lot in San Gabriel. A wiretap on a Chinese suspected narco in North Carolina named “Mimi” indicated that Sai Zhang had arranged to pick up a $300,000 drug cash payment outside the San Gabriel grocery. Hours later officers watched as a woman in a sleek blue Maserati leaned out and took a black bag — containing about $300,000 in cash — from the driver of a white Ram truck, a Hispanic man.
Gonzalez was well prepared, having spent months quietly briefing local police departments across Los Angeles County on the finely honed clockwork of the Chinese student’s network.
When the DEA called for backup, San Gabriel police launched. They tailed the big Ram truck for hours, weaving through LA’s dense murk until the truck finally stopped in a Compton parking lot. There, the driver transferred two boxes from a silver sedan into his truck. Moments later, officers swooped in, seizing 50 kilos of cocaine — concrete proof that the Chinese money trail led directly to narcotics.
Meanwhile, Steven Gonzalez, DEA’s lead detective, shadowed the blue Maserati east, far from Compton’s industrial edges, finally arriving in Temple City — a quiet suburban enclave in the western San Gabriel Valley, known for its large Chinese community and discreet residential streets. There, a person emerged with a bag and passed it to two women waiting in a car. When officers stopped her car, they found $25,000 in cash — dollars procured through Sai Zhang’s underground WeChat-based cash exchange.
The DEA team ultimately traced the white Ram truck — along with the same silver sedan that had delivered 50 kilos of cocaine to the Ram’s driver — back to a drug stash house in Rowland Heights. In December 2022, they intercepted another driver leaving that residence, seizing $500,000 in cash.
The next link in the Chinese-Sinaloa drug money chain closed the circle—from, in a sense, the Chinese student boss, Sai Zhang, down to his foot soldiers: Chinese exchange students in the United States, lured by the promise of easy spending money, and recruited through WeChat message boards to serve as money mules for organized crime.
These same students come from a vast pool of families whose North American tuition payments are themselves financed with laundered drug proceeds, weaving them even more tightly into fentanyl’s financial web.
A cinematic moment came on April 10, 2023. In the evening dusk officers watched a grocery bag of cash drop from a balcony belonging to one of Sai Zhang’s lieutenants. A Chinese man seen nervously pacing the sidewalk waiting for the bag drop scooped it up and drove off in a black Range Rover.
The Range Rover wound through Los Angeles, stopping at another pickup before heading to a quiet house in North Hills. There, the driver handed two bags to a tall young Chinese man — notable for his studious wire-frame glasses — waiting at the door.
Around midnight, officers knocked. An older woman nervously answered and led them to a bedroom. She told the officers she offered boarding to international exchange students. Under the bed, they found two grocery bags stuffed with $60,000 cash. The room belonged to a Chinese high-school student boarding in the home — a ground-level player in a global money chain, perhaps only vaguely aware, if at all, that their willingness to take “easy” money jobs in a parallel Chinese economy is driving overdose deaths and an overdue crackdown by American lawmakers.
In his affidavit, Steven Gonzales boils down the transnational model exposed by Zhang’s case in these terms: One method by which a Chinese businessman might purchase real estate in Los Angeles—while evading China’s strict currency export controls—involves acquiring U.S. dollars through an underground exchange. To do so, the businessman effectively “buys” dollars from a broker like Zhang who supplies drug cash already circulating in the United States.
In this arrangement, the Chinese investor transfers an equivalent amount of Chinese currency into a designated account in China controlled by the Mexican cartel. Once secured, those funds can then be used—legitimately on the surface—to settle debts owed by the cartel to Chinese manufacturers.
“The money in that account in China can legally be used to pay off legitimate debts to Chinese manufacturers who ship goods to Mexico,” U.S. court filings in Zhang’s indictment say.
The goods are shipped to Mexico, the DEA affidavit continues, where they are sold in the local market. The resulting pesos represent the final value of the drugs initially smuggled and sold in the United States, thereby closing the loop on the cartel’s illicit earnings and providing the Chinese investor with clean dollars to invest in U.S. assets.
Through this intricate scheme, the Chinese businessman successfully acquires the dollars needed to finance his Los Angeles property, while the Mexican traffickers are reimbursed for their American drug revenues.
Gonzales says that this scheme, known as trade-based money laundering, exploits legitimate international trade flows to conceal the movement of criminal proceeds—allowing transnational crime networks to move drugs across borders and launder and reintegrate illicit gains under the appearance of lawful commerce.
Invite your friends and earn rewards
The Belt and Road Driver: Don Im’s Analysis
For Don Im, the story of Zhang is far from new — just another chapter in a book he knows better than almost anyone. “We saw this going back to 2007, during the Zhenli Ye Gon era,” Im said. “It’s a bidding war. Whoever offers the highest price gets the drug dollars from North America and Europe.”
After listening to Don Im in hours of taped interviews, a metaphor suggests itself. China’s grip on the global economy — its underground and aboveground systems at work — is unimaginably complex. Black and white appear divided, but in fact are not. Like an Escher image maze, cash flows up, down, sideways — enters, exits, integrates, vanishes, reappears, reiterates. No exit, no end. A labyrinth of lies.
For this deep-dive story — to help explain the consequences to Western lawmakers, business leaders, and citizens affected by the fentanyl death crisis — Don Im provided sensitive details illustrating the scale and depth of money laundering and financial integration stemming from this narco economy.
“So you’re not seeing a direct, linear transfer of drug proceeds directly into China. You’ll see bulk cash being shipped. You’ll see money that’s placed and laundered within Canada or in the United States through local businesses. Then those funds are pulled into other accounts or investment vehicles—cryptocurrency, other so-called high-value assets, businesses, brick-and-mortar companies. And then they’re all sold again—homes as well.
And what’s that done? It’s offset with transfers of commodities that are equivalent to the millions of dollars or euros that are shipped from various companies in Guangzhou, where now you have, in those regions, thousands of Mexicans, Panamanians, and Colombians living and operating as their own diaspora with those Chinese manufacturing companies. Those companies are receiving orders from the Chinese businessmen in Mexico, Canada, Panama, Vancouver—requesting shipments of textiles, clothing, electronics, everyday products that the Chinese manufacture and we buy here and throughout the world.
And those are all equivalent to the amount of drug proceeds that the Chinese businessmen are buying in drug consumer countries. When I say North American consumer nations, I include Canada. Vancouver probably has the highest per capita overdose death rate in the world—the policy is insane there. So it’s essentially an indirect, asymmetric transfer of funds and value that has no direct correlation with, or link to, the drug proceeds that are generated off the streets—the heroin, the cocaine, the fentanyl, the marijuana, the methamphetamine.”
“They’ll deposit it into businesses and restaurants, and they’ll deposit those funds commingled with the legitimate funds they generate daily from restaurants, gas stations, convenience stores. And those will be deposited into numerous banks. Then the real drug proceeds—the profits—are transferred into a number of core accounts and pooled there. At that point, the owner in Mexico, Colombia, or Panama will decide where to send the money—to other accounts he controls.
Then he’ll go on WeChat and essentially enter one of those rooms—an auction for dollars. He’ll say, “Hey, listen, I’ve got a million in Vancouver, a million in New York, a million in Chicago—who wants to buy these?” And then you have Chinese citizens in China who are looking for dollars… to get their wealth out, or to pay off debt, or to get their kids into school elsewhere, or even to buy U.S. or Western products to ship into China. So they’ll bid—and they’ll pay a premium. Because what they’re doing is getting instructions to buy, say, a million dollars’ worth of commodities valued in Mexico, but in China it’s worth $800,000.”
Then the next time the cartel guy comes in and says, “Hey, I’ve got a million euros in Milan, Italy,” guess what? The Chinese businessman has the pesos to transfer to the cartel. So the Chinese businessman will pay $1.1 million—or a million dollars’ worth of renminbi or yuan—to ship internally in China to the manufacturing companies for all the commodities to be shipped to Mexico.
And once that’s shipped and the Chinese-Mexican businessman is satisfied with what he got, then he’ll say, “Okay, what do you want to do with the money in New York City?”
The Chinese businessman goes, “I want to look at a bunch of properties. I want you to send $200-some-thousand to New York University under the name of my son or nephew or niece.”
For those who might believe that China’s leaders are unaware of the global WeChat cash brokerage system — and its direct inputs into the Chinese factories powering Beijing’s mercantilist economy — Don Im offers a sobering set of facts.
“I brought it all together because I was running DEA’s money laundering operations at Special Operations Division, supporting undercover ops across the agency. DEA agents and analysts going back to the 2000’s tracked Mexicans and Colombians selling dollars to Chinese buyers. And they shared evidence with China law enforcement in circa 2012-2014.”
Im described even traveling to Beijing himself to brief the Ministry of Public Security.
“I personally went to Beijing in 2017, briefed top Ministry of Public Security officials. They listened when I explained how Chinese citizens use WeChat to buy drug dollars and then pay manufacturers in China to ship goods to brokers in Mexico. That was how the exchange happened.”
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
The Most Powerful People in the World
On June 26, leading Mexican cartel reporter Ioan Grillo posted this message to X: ‘You follow drugs, you get drug addicts and drug dealers. But you start to follow the money, and you don’t know where the f—k it’s gonna take you’ — from The Wire,” Grillo explained, “but also relevant to the historic orders by the U.S. Treasury against three Mexican banks, issued yesterday.”
Under the leadership of Treasury Secretary Scott Bessent, the U.S. formally sanctioned CIBanco, Intercam Banco, and Vector Casa de Bolsa on June 25, designating them “financial institutions of primary money-laundering concern.” The move effectively cuts these banks off from the U.S. financial system, citing their roles in laundering millions of dollars on behalf of Mexico’s most powerful cartels and facilitating payments for fentanyl precursor chemicals imported from China. The designations mark the first major use of new powers under the Fentanyl Sanctions Act.
For Don Im, this kind of action is long overdue — and, in his view, could probably go much farther and higher, into very discomforting areas for some world leaders.
A file called “Operation Heart of Stone” is illustrative. Im says he designed and ran this U.S. undercover operation targeting Horacio Cartes, Paraguay’s former president, who was accused of deep involvement in drug trafficking and money laundering. A 2010 U.S. State Department cable — leaked by WikiLeaks and derailing Heart of Stone’s momentum — labeled Cartes as the head of a major drug trafficking and laundering network. But, as Im points out, “we still got HSBC and hit them with a $1.9 billion fine.”
Speaking about this case and his decades spent infiltrating the world’s most dangerous criminal and financial networks, Im offered a set of opinions that — while carefully worded — amount to a kind of manifesto on who should be held accountable for opioid death tolls, and how to confront the system enabling them.
“Throughout the 1980s and 1990s, the DEA and US Customs (HSI) and IRS, had conducted numerous undercover money laundering operations against the drug cartels. Massive cash generated on the streets of North America and Europe were being deposited into thousands of banks,” Im said. “As a result, numerous anti-money laundering legislation efforts were implemented costing banks billions of dollars in compliance. At the same time, DEA, IRS and US Customs agents, established these money laundering operations by posing as money launderers and bankers to infiltrate the drug cartels.”
“These operations allowed law enforcement a door into the global underground banking system,” he continued. “DEA, USCS, IRS agents were able to track drug proceeds into the murky world where dirty cash was being cleaned by a global network of banks, businesses, law firms, NGO’s, corporations, offshore havens, philanthropic organizations, and reappearing into the accounts of corrupt government and politicians, millionaires and billionaires and their families.”
According to Im, it was DEA operations such as Swordfish, Pisces, Green Ice, Polar Cap, Casablanca, as well as Heart of Stone, Titan, and Green Treasure, that helped law enforcement capture evidence and intelligence into how the global system operates — with Sleeping Giant and Sai Zhang’s Chinese student and Sinaloa Cartel nexus being the latest sweeping case proving Im’s point.
“These investigations and similar investigations, led DEA to better understand how Chinese Money Laundering Organizations were leveraging trade, commerce, banking, technology and corruption to create a system of global bartering and unofficial banking,” Im said. “By using money to lure bad guys, and following the money upstream, DEA was able to seize billions of dollars of drug cash, seize and forfeit billions of dollars in assets purchased with drug proceeds, and even fine major banks such as Bank of America, Citibank, HSBC, Standard Charter, TD Bank, Wells Fargo, and many more. However, less than a handful of bank executives have ever been indicted and sent to prison.
Even with evidence, bankers, lawyers, accountants and politicians skirted prison sentences, while the low-hanging fruit drug traffickers were indicted and arrested. The judicial system is discriminatory when it comes to wealth, status and political convenience.”
The Bureau is a reader-supported publication.
To receive new posts and support my work, consider becoming a free or paid subscriber.
Invite your friends and earn rewards
Banks
Welcome Back, Wells Fargo!
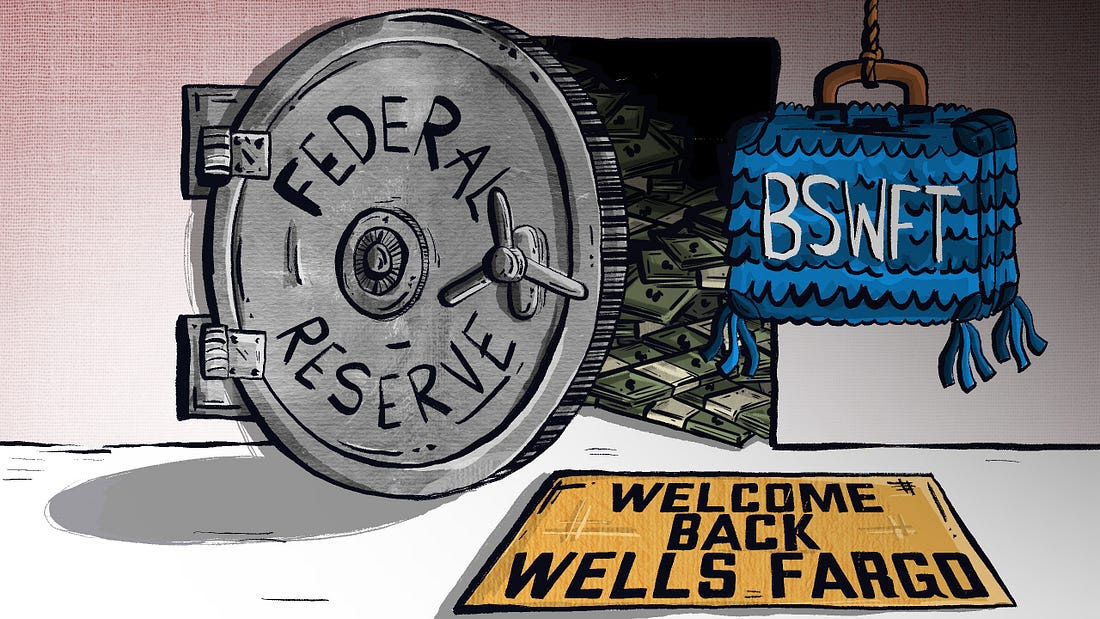
 Racket News
Racket News
By Eric Salzman
The heavyweight champion of financial crime gets seemingly its millionth chance to show it’s reformed
The past two decades have been tough ones for Wells Fargo and the many victims of its sprawling crime wave. While the banking industry is full of scammers, Wells took turning time honored street-hustles into multi-billion dollar white-collar hustles to a new level.
The Federal Reserve announced last month that Wells Fargo is no longer subject to the asset growth restriction the Fed finally enforced in 2018 after multiple scandals. This was a major enforcement action that prohibited Wells from growing existing loan portfolios, purchasing other bank branches or entering into any new activities that would result in their asset base growing.
Upon hearing the news that Wells was being released from the Fed’s penalty box, my mind turned to this pivotal moment in the classic movie “Slapshot.”
Here are some of Wells Fargo’s lowlights both before and after the Fed’s enforcement action:
- December 2022: Wells Fargo paid more than $2 billion to consumers and $1.7 billion in civil penalties after the Consumer Financial Protection Bureau (CFPB) found mismanagement — including illegal fees and interest charges — in several of its biggest product lines, such as auto loans, mortgages, and deposit accounts.
- September 2021: Wells Fargo paid $72.6 million to the Justice Department for overcharging foreign exchange customers from 2010-2017.
- February 2020: Wells Fargo paid $3 billion to settle criminal and civil investigations by the Justice Department and SEC into its aggressive sales practices between 2002 and 2016. About $500 million was eventually distributed to investors.
- January 2020: The Office of the Comptroller of the Currency (OCC) banned two senior executives, former CEO John Stumpf and ex-Head of Community Bank Carrie Tolstedt, from the banking industry. Stumpf and Tolstedt also incurred civil penalties of $17.5 million and $17 million.
- August 2018: The Justice Department levied a $2.09 billion fine on Wells Fargo for its actions during the subprime mortgage crisis, particularly its mortgage lending practices between 2005 and 2007.
- April 2018: Federal regulators at the CFPB and OCC examined Wells’ auto loan insurance and mortgage lending practices and ordered the bank to pay $1 billion in damages.
- February 2018: The aforementioned Fed enforcement action. In addition to the asset growth restriction, Wells was ordered to replace three directors.
- October 2017: Wells Fargo admitted wrongdoing after 110,000 clients were fined for missing a mortgage payment deadline — delays for which the bank was ultimately deemed at fault.
- July 2017: As many as 570,000 Wells Fargo customers were wrongly charged for auto insurance on car loans after the bank failed to verify whether those customers already had existing insurance. As a result, up to 20,000 customers may have defaulted on car loans.
- September 2016: Wells Fargo acknowledged its employees had created 1.5 million deposit accounts and 565,000 credit card accounts between 2002 and 2016 that “may not have been authorized by consumers,” according to CFPB. As a result, the lender was forced to pay $185 million in damages to the CFPB, OCC, and City and County of Los Angeles.
Additionally, somehow in 2023 Wells even managed to drop $1 billion in a civil settlement with shareholders for overstating their progress in complying with their 2018 agreement with the Fed to clean themselves up!
I imagine if Wells were in any other business, it wouldn’t be allowed to continue. But Wells is part of the “Too Big to Fail” club. Taking away its federal banking charter would be too disruptive for the financial markets, so instead they got what ended up being a seven-year growth ban. Not exactly rough justice.
While not the biggest settlement, my favorite Wells scam was the 2021 settlement of the seven-year pilfering operation, ripping off corporate customers’ foreign exchange transactions.
Like many banks, Wells Fargo offers its corporate clients with global operations foreign exchange (FX) services. For example, if a company is based in the U.S. but has extensive dealings in Canada, it may receive payments in Canadian dollars (CAD) that need to be exchanged for U.S. dollars (USD) and vice versa. Wells, like many banks, has foreign exchange specialists who do these conversions. Ideally, the banks optimize their clients’ revenue and decrease risk, in return for a markup fee, or “spread.”
There’s a lot of trust involved with this activity as the corporate customers generally have little idea where FX is trading minute by minute, nor do they know what time of day the actual orders for FX transactions — commonly called “BSwifts” — come in. For an unscrupulous bank, it’s a license to steal, which is exactly what Wells did.
According to the complaint, Wells regularly marked up transactions at higher spreads than what was agreed upon. This was just one of the variety of naughty schemes Wells used to clobber their customers. My two favorites were “The Big Figure Trick” and the “BSwift Pinata.”
The Big Figure Trick
Let’s say a client needs to sell USD for CAD, and that the $1 USD is worth $1.32 CAD. In banking parlance, the 32 cents is called the “Big Figure.” Wells would buy the CAD at $1.32 for $1 USD and then transpose the actual exchange rate on the customer statement from $1.32 to $1.23. If the customer didn’t notice, Wells would pocket the difference. On a transaction where the client is buying 5 million CAD with USD, the ill-gotten gain for Wells would be about $277,000 USD!
Conversely, if the customer did notice the difference, Wells would just blame it on the grunts in its operational back office, saying they accidentally transposed the number and “correct” the transaction. From the complaint, here is some give and take between two Wells FX specialists:
“You can play the transposition error game if you get called out.” Another FX sales specialist noted to a colleague about a previous transaction that a customer “didn’t flinch at the big fig the other day. Want to take a bit more?”
The BSwift Piñata
The way this hustle would work is, let’s say the Wells corporate customer was receiving payment from one of their Canadian clients. The Canadian client’s bank would send a BSwift message to Wells. The Wells client was in the dark about the U.S. dollar-Canadian dollar exchange rate because it had no idea what time of day the message arrived. Wells took advantage of that by purchasing U.S. dollars for Canadian dollars first. For simplicity, think of the U.S. dollar-Canadian dollar exchange rate as a widget that Wells bought for $1. If the widget increased in value, say to $1.10 during the day, Wells would sell the widget they purchased for $1 to the client for $1.10 and pocket 10 cents. If the price of the widget Wells bought for $1 fell to 95 cents, Wells would just give up their $1 purchase to the client, plus whatever markup they agreed to.
Heads, Wells wins. Tails, client loses.
The complaint notes that a Wells FX specialist wrote that he:
“Bumped spreads up a pinch,” that “these clients who are in the mode of just processing wires will most likely not notice this slight change in pricing” and that it “could have a very quick positive impact on revenue without a lot of risk.”
Talk about a boiler room operation. Personally, I think calling what you are doing to a client a “piñata” should have easily put Wells in the Fed’s penalty box another 5 years at least!
Wells has been released from the Fed’s 2018 enforcement order. I would like to think they have learned their lesson and are reformed, but I would lay good odds against it. A leopard can’t change its spots.
Racket News is a reader-supported publication.
Consider becoming a free or paid subscriber.
-

 Agriculture2 days ago
Agriculture2 days agoCanada’s supply management system is failing consumers
-

 Economy2 days ago
Economy2 days agoTrump opens door to Iranian oil exports
-

 Alberta1 day ago
Alberta1 day agoCOVID mandates protester in Canada released on bail after over 2 years in jail
-

 Business1 day ago
Business1 day agoCanada’s loyalty to globalism is bleeding our economy dry
-

 armed forces23 hours ago
armed forces23 hours agoCanada’s Military Can’t Be Fixed With Cash Alone
-

 Crime1 day ago
Crime1 day agoProject Sleeping Giant: Inside the Chinese Mercantile Machine Linking Beijing’s Underground Banks and the Sinaloa Cartel
-

 Alberta1 day ago
Alberta1 day agoAlberta uncorks new rules for liquor and cannabis
-
 Business1 day ago
Business1 day agoCarney’s spending makes Trudeau look like a cheapskate








