Crime
Public information and warning: Violent offender released

Public information and warning: Violent offender released
From EPS
Edmonton: In the interest of public safety, the Edmonton Police Service is issuing the following warning; Kelly Weir is a convicted violent offender, and the Edmonton Police Service has reasonable grounds to believe he will commit another violent offence against someone while in the community.
Weir will be residing in the Edmonton area. The Edmonton Police Service is seeking a court order on Weir and he will be monitored by the Behavioural Assessment Unit of the Edmonton Police Service.
Weir’s risk of offending behavior increases significantly if under the influence of intoxicants, especially alcohol.
Weir’s violent offences often result in physical harm to his victims and he has been known to carry and utilize weapons in the commission of his offences, especially a knife. Weir is quick to anger, especially if he perceives being challenged, which can escalate to violence very quickly, especially if he is intoxicated. This anger and violence can be directed at anyone that he comes into contact with in the community.
Weir has been placed on a series of court ordered conditions including:
- He must live at a residence approved by the Provincial Court or his supervisor and must not change that address until he has received written approval from his supervisor.
- He must abide by a curfew of 10 p.m. to 6 a.m. daily unless a varied time is approved in writing by his supervisor.
- He will not have any guests at his residence during his hours of curfew unless they have been identified and approved by his supervisor.
- He shall not purchase, possess or consume any alcoholic beverages or cannabis products. He shall not consume or possess any drug listed in the schedules of the Controlled Drugs and Substances Act, any prescription drugs not prescribed to him, or any other intoxicating substances.
- He must not have or allow any other person to have alcohol or cannabis products at his place of residence.
- He must not possess any drug paraphernalia such as crack or marijuana pipes, self-made pipes of any kind, e-cigarettes, bongs, water pipes, cigarette papers, rolling papers, or syringes.
- He must not be in any licensed premise other than a dining room for the sole purpose of having a meal. He must not attend at any liquor store or cannabis dispensary.
- He must not travel out of the City of Edmonton without written approval of his supervisor or the Provincial Court of Alberta.
- He must not be in possession of weapons of any kind, including knives, except in his residence or at a restaurant for the sole purpose of consuming a meal, bear spray or dog spray, firearms, ammunition, explosive material, or any weapons whether homemade or otherwise.
Anyone with any information about any potential breaches of these conditions by Weir can contact the EPS at 780-423-4567.
The Edmonton Police Service is issuing this information and warning after careful deliberation of all related issues, including privacy concerns, in the belief that it is clearly in the public interest to inform the members of the community.
Kelly Samuel Weir, 55
Height: 6’1”
Weight: 195 lbs
Eyes: brown
Hair: black/grey
Members of the public are advised that the intent of this process is to enable citizens to take suitable precautionary measures. Releasing this information is NOT intended to encourage people to engage in any form of vigilante action.
Crime
National Health Care Fraud Takedown Results in 324 Defendants Charged in Connection with Over $14.6 Billion in Alleged Fraud
A 50-district dragnet uncovers transnational fraud, AI-driven deception, and systemic theft from Medicare, Medicaid, and U.S. taxpayers totaling over $14.6 billion
The Department of Justice announced Monday the outcome of the 2025 National Health Care Fraud Takedown, the largest coordinated enforcement action against health care fraud in U.S. history. Federal prosecutors have filed criminal charges against 324 individuals across 50 federal judicial districts and 12 State Attorneys General’s Offices, including 96 licensed medical professionals—among them doctors, nurse practitioners, and pharmacists. The defendants stand accused of orchestrating fraudulent schemes amounting to more than $14.6 billion in intended losses to Medicare, Medicaid, and other federally funded programs.

This historic enforcement action more than doubles the previous national record of $6 billion. As part of this effort, federal and state authorities have seized over $245 million in cash, luxury vehicles, cryptocurrency, and other high-value assets. The Centers for Medicare & Medicaid Services (CMS) separately reported that it successfully prevented more than $4 billion in fraudulent payments in the months leading up to the Takedown. CMS also confirmed that it suspended or revoked the billing privileges of 205 providers linked to fraudulent activity. In the civil domain, federal agencies filed actions against 20 defendants tied to $14.2 million in alleged fraud and finalized civil settlements with an additional 106 defendants, totaling $34.3 million in recovered funds.
The Takedown was led by the Health Care Fraud Unit of the DOJ Criminal Division’s Fraud Section and carried out in close coordination with U.S. Attorneys’ Offices nationwide, the Department of Health and Human Services Office of Inspector General (HHS-OIG), the Federal Bureau of Investigation (FBI), the Drug Enforcement Administration (DEA), and multiple state law enforcement agencies. Medicaid Fraud Control Units in 18 states also played a central role in investigating and prosecuting the cases.
In remarks accompanying the announcement, Secretary of Health and Human Services Robert F. Kennedy Jr. emphasized that the agency would aggressively work with law enforcement to eliminate the “pervasive health care fraud that drove up costs and harmed patients under the former administration.” Attorney General Pamela Bondi echoed the urgency, calling the action “justice delivered to those who steal from taxpayers and endanger lives.” Matthew R. Galeotti, head of the Justice Department’s Criminal Division, underscored the gravity of the crimes targeted, noting that fraudulent schemes often lead not only to financial losses but also to direct patient harm, including medically unnecessary procedures and worsened addiction outcomes.
FBI Director Kash Patel emphasized that this Takedown represents the largest in the bureau’s history, highlighting the theft of more than $13 billion from federal health programs. Acting Inspector General Juliet T. Hodgkins of HHS-OIG described the scale of harm as unprecedented and reaffirmed the agency’s commitment to safeguarding the public.
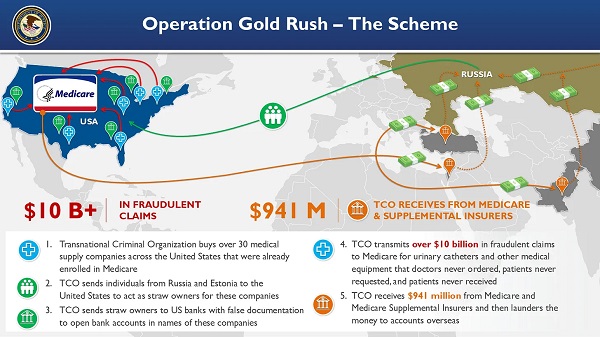
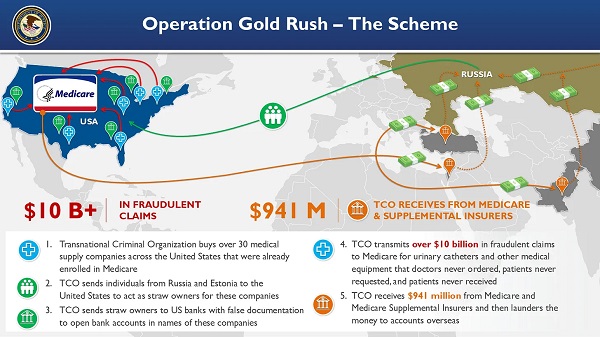
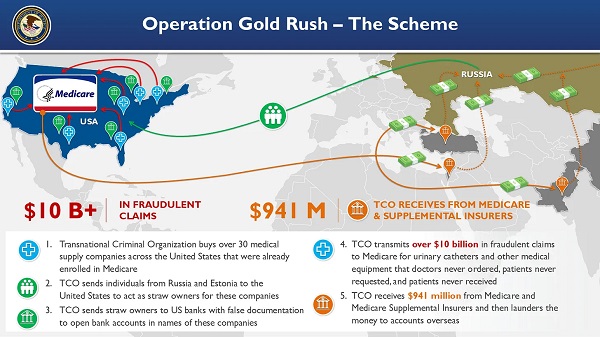
Among the most significant components of this national operation was Operation Gold Rush, which uncovered a sophisticated transnational conspiracy responsible for over $10 billion in fraudulent Medicare claims. The scheme was orchestrated by foreign nationals who, acting as a coordinated criminal enterprise, acquired more than 30 medical supply companies across the United States. These companies had already been enrolled in Medicare, and were then used to funnel false claims for urinary catheters and other durable medical equipment. Stolen identities of over one million Americans were used to submit these claims, which had not been requested by patients, nor ordered by physicians.
The conspiracy relied on straw owners sent from Russia and Estonia to the U.S., who were directed by co-conspirators communicating through encrypted channels. Using fraudulent documentation, these straw owners opened U.S. bank accounts for laundering proceeds. Though the organization submitted over $10.6 billion in claims, CMS successfully blocked most of the payments. Only approximately $41 million reached the conspirators via Medicare, but approximately $900 million was disbursed by Medicare supplemental insurers before the fraud was detected.
Four individuals were arrested in Estonia and eight others were apprehended at major U.S. airports and border crossings as they attempted to flee. Law enforcement seized approximately $27.7 million in fraud proceeds from this operation.

Federal prosecutors filed related charges in five districts: the Central District of California, the Middle District of Florida, the Northern District of Illinois, the District of New Jersey, and the Eastern District of New York.
In a separate scheme centered in Illinois, the Department brought charges against five individuals, including two executives from Pakistani marketing firms, who used artificial intelligence to generate fake audio recordings of Medicare beneficiaries purporting to consent to receive medical equipment. This fraudulent data was sold to laboratories and equipment suppliers, which used it to file $703 million in false claims. Approximately $418 million was ultimately paid out on these claims, and the government has so far seized $44.7 million in related assets. The fraud involved not only AI-based deception but also the illegal sale and laundering of stolen personal health information.
Another case exposed a billing company executive based in Pakistan and the United Arab Emirates who conspired with addiction treatment centers to submit approximately $650 million in fraudulent claims to Arizona Medicaid. Some services billed were never rendered, and others were so deficient as to provide no therapeutic value. The operation targeted vulnerable individuals, including members of Native American tribes and the homeless. Kickbacks were paid for patient referrals, and the executive used at least $25 million in illicit funds to purchase a $2.9 million home in Dubai.

The Department also charged 49 defendants in connection with over $1.17 billion in fraudulent claims tied to telemedicine and genetic testing. In one Florida case, an owner of both telemedicine and durable medical equipment companies orchestrated a $46 million scheme involving deceptive telemarketing campaigns that generated unauthorized genetic testing and equipment claims. The Department continues to prioritize cases involving telehealth-based fraud, which often exploits unwitting patients through misrepresented or manufactured consent.
Prescription opioid diversion was another central focus of the Takedown. A total of 74 defendants, including 44 licensed medical professionals, were charged across 58 criminal cases for illegally distributing more than 15 million opioid pills. One Texas pharmacy alone was responsible for over 3 million of these pills, which included highly addictive substances such as oxycodone, hydrocodone, and carisoprodol. The DEA concurrently announced 93 administrative actions to revoke licenses and registrations of pharmacies and providers implicated in the unlawful handling of controlled substances.
Other cases include a $28.7 million scheme in Tennessee involving medications falsely billed to the Federal Employees’ Compensation Fund, where prescriptions were neither authorized by physicians nor dispensed as claimed. In separate indictments filed in Washington and California, medical providers were charged with stealing fentanyl and hydrocodone intended for pediatric patients under anesthesia.
The geographic scope of the Takedown was vast. In total, 189 federal cases were filed across all 50 federal judicial districts, and 91 state-level cases were brought in 12 states by participating Attorneys General. This unprecedented coordination underscores the national impact and bipartisan support for rooting out fraud in American health care systems.
To enhance ongoing efforts, the Department also announced the establishment of a new Health Care Fraud Data Fusion Center.

This joint initiative brings together specialists from the DOJ’s Health Care Fraud Unit, HHS-OIG, FBI, and CMS to leverage cloud computing, artificial intelligence, and large-scale data analytics to detect emergent fraud patterns. The Fusion Center aligns with Executive Order 14243, “Stopping Waste, Fraud, and Abuse by Eliminating Information Silos,” which mandates interagency cooperation and data-sharing to reduce redundancy and increase efficiency in enforcement.
Principal Assistant Deputy Chief Jacob Foster, Assistant Deputy Chief Rebecca Yuan, Trial Attorney Miriam L. Glaser Dauermann, and Data Analyst Elizabeth Nolte coordinated this year’s Takedown from within the DOJ’s Health Care Fraud Unit. Prosecutors from the National Rapid Response team and regional Strike Forces in 27 districts led casework alongside U.S. Attorneys’ Offices and 18 state Medicaid Fraud Control Units. Additional support came from the Department of Labor, VA-OIG, IRS Criminal Investigation, Homeland Security Investigations, the Defense Criminal Investigative Service, the Office of Personnel Management, the United States Postal Service OIG, and numerous other federal and local agencies.
Image sources: US DOJ
Crime
Suspected ambush leaves two firefighters dead in Idaho

Quick Hit:
Two firefighters were killed and another wounded Sunday after a gunman opened fire on first responders tackling a blaze near Coeur d’Alene, Idaho. The shooter was later found dead, and authorities believe the fire may have been set to lure crews into an ambush.
Key Details:
- The ambush began around 2 p.m. local time as fire crews arrived at a brush fire and were met with sniper-style gunfire from a wooded area.
- SWAT teams located the deceased suspect roughly five hours later, with a weapon nearby. His identity has not yet been released.
- The Kootenai County Sheriff said the ongoing fire could not be addressed during the gunfight, calling the attack a “heinous direct assault” on first responders.
Diving Deeper:
A deadly ambush on Sunday afternoon left two Idaho firefighters dead and a third injured after they were shot while attempting to contain a brush fire on Canfield Mountain. The surprise attack reportedly began around 2 p.m., when bullets suddenly rained down on emergency crews from hidden positions in the wooded terrain near Coeur d’Alene.
Authorities now believe the blaze may have been deliberately set as bait. Kootenai County Sheriff Bob Norris described the situation as “an active sniper attack,” saying the scene quickly escalated into chaos with gunfire coming from multiple directions.
“We don’t know if there’s one, two, three or four [shooters],” Norris said in an early evening press conference. “I’m hoping that someone has a clear shot and is able to neutralize [the suspect], because they’re not showing any signs of surrendering.”
Roughly five hours after the first shots were fired, SWAT officers found a body next to a firearm along the Canfield Mountain Trail. Authorities have not confirmed whether the individual was the sole assailant, nor have they publicly identified the person. The FBI, along with state and local agencies, had been deployed to the scene to assist with the operation.
The two firefighters who died have not yet been named. The third, who sustained a gunshot wound, was transported to Kootenai Health and remains hospitalized. His current condition is unknown.
The firefight effectively halted efforts to contain the brush fire, which remained active late into Sunday. “It’s going to keep burning. We can’t put any resources on it right now,” Norris said during the standoff. Shelter-in-place orders were issued for the surrounding area, including the popular Canfield Mountain Trailhead, but those restrictions were lifted after the suspect was found dead.
Idaho Governor Brad Little reacted to the tragedy on social media, calling the ambush “a heinous direct assault on our brave firefighters.” He added, “Teresa and I are heartbroken. I ask all Idahoans to pray for them and their families as we wait to learn more.”
Federal and local officials are continuing to investigate the incident, including the origins of the fire and whether additional suspects may have been involved.
-

 Business2 days ago
Business2 days agoCanada Caves: Carney ditches digital services tax after criticism from Trump
-

 Alberta1 day ago
Alberta1 day agoAlberta judge sides with LGBT activists, allows ‘gender transitions’ for kids to continue
-
 Crime20 hours ago
Crime20 hours agoNational Health Care Fraud Takedown Results in 324 Defendants Charged in Connection with Over $14.6 Billion in Alleged Fraud
-

 Business8 hours ago
Business8 hours agoElon Musk slams Trump’s ‘Big Beautiful Bill,’ calls for new political party
-

 Censorship Industrial Complex8 hours ago
Censorship Industrial Complex8 hours agoGlobal media alliance colluded with foreign nations to crush free speech in America: House report
-

 Crime2 days ago
Crime2 days agoSuspected ambush leaves two firefighters dead in Idaho
-

 Business2 days ago
Business2 days agoMassive government child-care plan wreaking havoc across Ontario
-

 Alberta1 day ago
Alberta1 day agoAlberta Independence Seekers Take First Step: Citizen Initiative Application Approved, Notice of Initiative Petition Issued

 By
By 





